搜索到
51
篇与
的结果
-
 OpenVPN-配置文件 1. Openvpn Server 端配置文件################################################# # Sample OpenVPN 2.0 config file for # # multi-client server. # # # # This file is for the server side # # of a many-clients <-> one-server # # OpenVPN configuration. # # # # OpenVPN also supports # # single-machine <-> single-machine # # configurations (See the Examples page # # on the web site for more info). # # # # This config should work on Windows # # or Linux/BSD systems. Remember on # # Windows to quote pathnames and use # # double backslashes, e.g.: # # "C:\\Program Files\\OpenVPN\\config\\foo.key" # # # # Comments are preceded with '#' or ';' # ################################################# # Which local IP address should OpenVPN # listen on? (optional) ;local a.b.c.d # Which TCP/UDP port should OpenVPN listen on? # If you want to run multiple OpenVPN instances # on the same machine, use a different port # number for each one. You will need to # open up this port on your firewall. port 1194 # TCP or UDP server? proto tcp ;proto udp # "dev tun" will create a routed IP tunnel, # "dev tap" will create an ethernet tunnel. # Use "dev tap0" if you are ethernet bridging # and have precreated a tap0 virtual interface # and bridged it with your ethernet interface. # If you want to control access policies # over the VPN, you must create firewall # rules for the the TUN/TAP interface. # On non-Windows systems, you can give # an explicit unit number, such as tun0. # On Windows, use "dev-node" for this. # On most systems, the VPN will not function # unless you partially or fully disable # the firewall for the TUN/TAP interface. ;dev tap dev tun # Windows needs the TAP-Win32 adapter name # from the Network Connections panel if you # have more than one. On XP SP2 or higher, # you may need to selectively disable the # Windows firewall for the TAP adapter. # Non-Windows systems usually don't need this. ;dev-node MyTap # SSL/TLS root certificate (ca), certificate # (cert), and private key (key). Each client # and the server must have their own cert and # key file. The server and all clients will # use the same ca file. # # See the "easy-rsa" directory for a series # of scripts for generating RSA certificates # and private keys. Remember to use # a unique Common Name for the server # and each of the client certificates. # # Any X509 key management system can be used. # OpenVPN can also use a PKCS #12 formatted key file # (see "pkcs12" directive in man page). ca /etc/openvpn/certs/ca.crt cert /etc/openvpn/certs/server.crt key /etc/openvpn/certs/server.key # This file should be kept secret # Diffie hellman parameters. # Generate your own with: # openssl dhparam -out dh2048.pem 2048 #dh dh2048.pem dh /etc/openvpn/certs/dh.pem # Network topology # Should be subnet (addressing via IP) # unless Windows clients v2.0.9 and lower have to # be supported (then net30, i.e. a /30 per client) # Defaults to net30 (not recommended) ;topology subnet # Configure server mode and supply a VPN subnet # for OpenVPN to draw client addresses from. # The server will take 10.8.0.1 for itself, # the rest will be made available to clients. # Each client will be able to reach the server # on 10.8.0.1. Comment this line out if you are # ethernet bridging. See the man page for more info. server 10.8.0.0 255.255.255.0 # Maintain a record of client <-> virtual IP address # associations in this file. If OpenVPN goes down or # is restarted, reconnecting clients can be assigned # the same virtual IP address from the pool that was # previously assigned. ifconfig-pool-persist /var/log/openvpn/ipp.txt # Configure server mode for ethernet bridging. # You must first use your OS's bridging capability # to bridge the TAP interface with the ethernet # NIC interface. Then you must manually set the # IP/netmask on the bridge interface, here we # assume 10.8.0.4/255.255.255.0. Finally we # must set aside an IP range in this subnet # (start=10.8.0.50 end=10.8.0.100) to allocate # to connecting clients. Leave this line commented # out unless you are ethernet bridging. ;server-bridge 10.8.0.4 255.255.255.0 10.8.0.50 10.8.0.100 # Configure server mode for ethernet bridging # using a DHCP-proxy, where clients talk # to the OpenVPN server-side DHCP server # to receive their IP address allocation # and DNS server addresses. You must first use # your OS's bridging capability to bridge the TAP # interface with the ethernet NIC interface. # Note: this mode only works on clients (such as # Windows), where the client-side TAP adapter is # bound to a DHCP client. ;server-bridge # Push routes to the client to allow it # to reach other private subnets behind # the server. Remember that these # private subnets will also need # to know to route the OpenVPN client # address pool (10.8.0.0/255.255.255.0) # back to the OpenVPN server. ;push "route 192.168.10.0 255.255.255.0" ;push "route 192.168.20.0 255.255.255.0" # To assign specific IP addresses to specific # clients or if a connecting client has a private # subnet behind it that should also have VPN access, # use the subdirectory "ccd" for client-specific # configuration files (see man page for more info). # EXAMPLE: Suppose the client # having the certificate common name "Thelonious" # also has a small subnet behind his connecting # machine, such as 192.168.40.128/255.255.255.248. # First, uncomment out these lines: ;client-config-dir ccd ;route 192.168.40.128 255.255.255.248 # Then create a file ccd/Thelonious with this line: # iroute 192.168.40.128 255.255.255.248 # This will allow Thelonious' private subnet to # access the VPN. This example will only work # if you are routing, not bridging, i.e. you are # using "dev tun" and "server" directives. # EXAMPLE: Suppose you want to give # Thelonious a fixed VPN IP address of 10.9.0.1. # First uncomment out these lines: ;client-config-dir ccd ;route 10.9.0.0 255.255.255.252 # Then add this line to ccd/Thelonious: # ifconfig-push 10.9.0.1 10.9.0.2 # Suppose that you want to enable different # firewall access policies for different groups # of clients. There are two methods: # (1) Run multiple OpenVPN daemons, one for each # group, and firewall the TUN/TAP interface # for each group/daemon appropriately. # (2) (Advanced) Create a script to dynamically # modify the firewall in response to access # from different clients. See man # page for more info on learn-address script. ;learn-address ./script # If enabled, this directive will configure # all clients to redirect their default # network gateway through the VPN, causing # all IP traffic such as web browsing and # and DNS lookups to go through the VPN # (The OpenVPN server machine may need to NAT # or bridge the TUN/TAP interface to the internet # in order for this to work properly). ;push "redirect-gateway def1 bypass-dhcp" push "redirect-gateway def1" # Certain Windows-specific network settings # can be pushed to clients, such as DNS # or WINS server addresses. CAVEAT: # http://openvpn.net/faq.html#dhcpcaveats # The addresses below refer to the public # DNS servers provided by opendns.com. ;push "dhcp-option DNS 208.67.222.222" ;push "dhcp-option DNS 208.67.220.220" push "dhcp-option DNS 8.8.8.8" push "dhcp-option DNS 8.8.8.4" # Uncomment this directive to allow different # clients to be able to "see" each other. # By default, clients will only see the server. # To force clients to only see the server, you # will also need to appropriately firewall the # server's TUN/TAP interface. client-to-client # Uncomment this directive if multiple clients # might connect with the same certificate/key # files or common names. This is recommended # only for testing purposes. For production use, # each client should have its own certificate/key # pair. # # IF YOU HAVE NOT GENERATED INDIVIDUAL # CERTIFICATE/KEY PAIRS FOR EACH CLIENT, # EACH HAVING ITS OWN UNIQUE "COMMON NAME", # UNCOMMENT THIS LINE OUT. ;duplicate-cn # The keepalive directive causes ping-like # messages to be sent back and forth over # the link so that each side knows when # the other side has gone down. # Ping every 10 seconds, assume that remote # peer is down if no ping received during # a 120 second time period. keepalive 10 120 # For extra security beyond that provided # by SSL/TLS, create an "HMAC firewall" # to help block DoS attacks and UDP port flooding. # # Generate with: # openvpn --genkey --secret ta.key # # The server and each client must have # a copy of this key. # The second parameter should be '0' # on the server and '1' on the clients. tls-auth /etc/openvpn/server/certs/ta.key 0 # This file is secret # Select a cryptographic cipher. # This config item must be copied to # the client config file as well. # Note that v2.4 client/server will automatically # negotiate AES-256-GCM in TLS mode. # See also the ncp-cipher option in the manpage cipher AES-256-CBC # Enable compression on the VPN link and push the # option to the client (v2.4+ only, for earlier # versions see below) ;compress lz4-v2 ;push "compress lz4-v2" # For compression compatible with older clients use comp-lzo # If you enable it here, you must also # enable it in the client config file. ;comp-lzo # The maximum number of concurrently connected # clients we want to allow. ;max-clients 100 # It's a good idea to reduce the OpenVPN # daemon's privileges after initialization. # # You can uncomment this out on # non-Windows systems. ;user nobody ;group nogroup # The persist options will try to avoid # accessing certain resources on restart # that may no longer be accessible because # of the privilege downgrade. persist-key persist-tun # Output a short status file showing # current connections, truncated # and rewritten every minute. status /var/log/openvpn/openvpn-status.log # By default, log messages will go to the syslog (or # on Windows, if running as a service, they will go to # the "\Program Files\OpenVPN\log" directory). # Use log or log-append to override this default. # "log" will truncate the log file on OpenVPN startup, # while "log-append" will append to it. Use one # or the other (but not both). ;log /var/log/openvpn/openvpn.log ;log-append /var/log/openvpn/openvpn.log # Set the appropriate level of log # file verbosity. # # 0 is silent, except for fatal errors # 4 is reasonable for general usage # 5 and 6 can help to debug connection problems # 9 is extremely verbose verb 3 # Silence repeating messages. At most 20 # sequential messages of the same message # category will be output to the log. ;mute 20 # Notify the client that when the server restarts so it # can automatically reconnect. explicit-exit-notify 0 crl-verify /etc/openvpn/easyrsa/pki/crl.pem1. Openvpn Client 端配置文件############################################## # Sample client-side OpenVPN 2.0 config file # # for connecting to multi-client server. # # # # This configuration can be used by multiple # # clients, however each client should have # # its own cert and key files. # # # # On Windows, you might want to rename this # # file so it has a .ovpn extension # ############################################## # Specify that we are a client and that we # will be pulling certain config file directives # from the server. client # Use the same setting as you are using on # the server. # On most systems, the VPN will not function # unless you partially or fully disable # the firewall for the TUN/TAP interface. ;dev tap dev tun # Windows needs the TAP-Win32 adapter name # from the Network Connections panel # if you have more than one. On XP SP2, # you may need to disable the firewall # for the TAP adapter. ;dev-node MyTap # Are we connecting to a TCP or # UDP server? Use the same setting as # on the server. proto tcp ;proto udp # The hostname/IP and port of the server. # You can have multiple remote entries # to load balance between the servers. remote my-server-1 1194 ;remote my-server-2 1194 # Choose a random host from the remote # list for load-balancing. Otherwise # try hosts in the order specified. ;remote-random # Keep trying indefinitely to resolve the # host name of the OpenVPN server. Very useful # on machines which are not permanently connected # to the internet such as laptops. resolv-retry infinite # Most clients don't need to bind to # a specific local port number. nobind # Downgrade privileges after initialization (non-Windows only) ;user nobody ;group nogroup # Try to preserve some state across restarts. persist-key persist-tun # If you are connecting through an # HTTP proxy to reach the actual OpenVPN # server, put the proxy server/IP and # port number here. See the man page # if your proxy server requires # authentication. ;http-proxy-retry # retry on connection failures ;http-proxy [proxy server] [proxy port #] # Wireless networks often produce a lot # of duplicate packets. Set this flag # to silence duplicate packet warnings. ;mute-replay-warnings # SSL/TLS parms. # See the server config file for more # description. It's best to use # a separate .crt/.key file pair # for each client. A single ca # file can be used for all clients. ca ca.crt cert username.crt key username.key # Verify server certificate by checking that the # certicate has the correct key usage set. # This is an important precaution to protect against # a potential attack discussed here: # http://openvpn.net/howto.html#mitm # # To use this feature, you will need to generate # your server certificates with the keyUsage set to # digitalSignature, keyEncipherment # and the extendedKeyUsage to # serverAuth # EasyRSA can do this for you. remote-cert-tls server # If a tls-auth key is used on the server # then every client must also have the key. tls-auth ta.key 1 # Select a cryptographic cipher. # If the cipher option is used on the server # then you must also specify it here. # Note that v2.4 client/server will automatically # negotiate AES-256-GCM in TLS mode. # See also the ncp-cipher option in the manpage cipher AES-256-CBC # Enable compression on the VPN link. # Don't enable this unless it is also # enabled in the server config file. #comp-lzo # Set log file verbosity. verb 3 # Silence repeating messages ;mute 203. Openvpn APP 配置[Tips] IOS客户端配置client dev tun ;proto tcp proto udp remote xxx.xxx.xxx.xxx 1194 resolv-retry infinite nobind persist-key persist-tun mute-replay-warnings #ca ca.crt #cert client02.crt #key client02.key remote-cert-tls server #tls-auth ta.key 1 #comp-lzo verb 3 <ca> -----BEGIN CERTIFICATE----- MIIDJDCCAgygAwIBAgIJAMv+3UPUdlJjMA0GCSqGSIb3DQEBCwUAMBExDzANBgNV BAMMBnNlcnZlcjAeFw0yMjA0MjEwOTEzNDJaFw0zMjA0MTgwOTEzNDJaMBExDzAN BgNVBAMMBnNlcnZlcjCCASIwDQYJKoZIhvcNAQEBBQADggEPADCCAQoCggEBAJ3n HQJcnsmqkPJwLEV8YymrH1l7189/sXmJ0sa5mIYIcBKKL5haAQ6rdjRlJtuTDnoA oFJ1+Uf9Qwpxs/Tj4blsfewsSD5WlXGq2htgXZv8jjIiKwpSjN2LImJi0pOuow/v nFYGA58Xtsg4EDCIGF5LWc8L0WdfmkvN+LFvUQtnlzyIJ1haHFJdCNtgxpj8Khsa GDDRX7Nr4abnTAQwEb6jcReAhvrqu/b5CtgQDYBHV6pY1toXwZ8PzFnay4ngQFJA 5KUoFsso4beHl/F7u4O44CH61rJwiPavRKBwbYZt6ySU7mQkJRC1yQkRNV4HKwdB 6DOBdmZ+CDJSfMbkpysCAwEAAaN/MH0wHQYDVR0OBBYEFLcvJFbXdouS61U7FQ+d OTmjS20JMEEGA1UdIwQ6MDiAFLcvJFbXdouS61U7FQ+dOTmjS20JoRWkEzARMQ8w DQYDVQQDDAZzZXJ2ZXKCCQDL/t1D1HZSYzAMBgNVHRMEBTADAQH/MAsGA1UdDwQE AwIBBjANBgkqhkiG9w0BAQsFAAOCAQEAQt6Qxbp2sNc/WtRY7jhLl7J52kMzpoO/ 5MWmqoHZ4IU1yM9hN3KzJIby0d0JgzlWAPvl74RnV3Padu5xSlYeCK8y+EOKuJXx b/CXPloHET5EcGLpZWnhFzTUrG68QUAeP3mwP+rr+2/RTSoYNq8Qu5r8npHjhr40 xH+dLtBZDAOLJcKgi4lgCu8WINCMgPwDd5hAsGD1ul7Lso3xGlHJePt6pV2tM45e BD8vhF59WpShIRYlLqWbRG9glB7IFws024jefCEThSXuPt5M6cSO15pqDkeSjG25 CNtvgMw+VSFeBzvs2hEgY8x08pU2EPn1lhmfolcmRVdg8i0qnJBpRg== -----END CERTIFICATE----- </ca> <cert> -----BEGIN CERTIFICATE----- MIIDQjCCAiqgAwIBAgIRANLIdjgXLZIM++/mhxiBLRYwDQYJKoZIhvcNAQELBQAw ETEPMA0GA1UEAwwGc2VydmVyMB4XDTIyMDQyMTEyNTEwOVoXDTI0MDcyNDEyNTEw OVowEzERMA8GA1UEAwwIY2xpZW50MDIwggEiMA0GCSqGSIb3DQEBAQUAA4IBDwAw ggEKAoIBAQDJgm94AHU2P8NpTTuPIDLCQxT3fqJafi/67Yy2LgTAbif+C/9aUuXC M/wJ4fUcBej82+oga583wfwSECubxAaiJc6hJ8fnXUQ7ZPL4PSUCu8QCCFaJCjMC 1nv8DjCC6R9YX7tAzcWOv3z8kz2Ci4elzQCm1oyhxKJKPAUoANtDPO2/8z2vNmWA 01nMsz3ehWADpVto0WWHM2o1ZCE+Mihx20rSL0c3P1IMWqoXdEllo3E10Tl/d1I1 tPY0DQ/t6BjTSUnmbto41rGHat/sarpg4sznuA1eU+wbJbF0/3kAmK8GRdelGLjs Veq0EWIc5QfU7TAl+majz5cBEp8Lh8gNAgMBAAGjgZIwgY8wCQYDVR0TBAIwADAd BgNVHQ4EFgQUUgrZwhdjvyyLaMdexvU32gKz/+4wQQYDVR0jBDowOIAUty8kVtd2 i5LrVTsVD505OaNLbQmhFaQTMBExDzANBgNVBAMMBnNlcnZlcoIJAMv+3UPUdlJj MBMGA1UdJQQMMAoGCCsGAQUFBwMCMAsGA1UdDwQEAwIHgDANBgkqhkiG9w0BAQsF AAOCAQEAl07HOolF0Hos9oHfcQlztWt+WNHKQBQ/FxVjufwYv8cZRu+eZozrZvZe fA4mgzvPXsDRZlLKqL4zLhsGyEUTcjAdvhh0s7PVqgppWN1pLEozTvhgJ8r8L8ev fRXf7R0bJHPzzqFdBzdnFhZ3D4fnDafEFlXfqpl30TdEP50CRjYHk1U+0PWyl3+l 05SBCvNaF0nrK+gD2VDtIHp17nB6LFdpW03sBmkLCVy9KDhk1Z0zwtoJe8RI98sj 2r/7ApuXh6otEJlaFKZ0ChotJL4QEBM5nVOJNFWCvu34KXJevkhRQYTwlKsjgfDN eDOvxAOxozI1HegVavrl8K70iFUhQw== -----END CERTIFICATE----- </cert> <key> -----BEGIN PRIVATE KEY----- MIIEvgIBADANBgkqhkiG9w0BAQEFAASCBKgwggSkAgEAAoIBAQDJgm94AHU2P8Np TTuPIDLCQxT3fqJafi/67Yy2LgTAbif+C/9aUuXCM/wJ4fUcBej82+ogDwnyIzPe IrubxAaiJc6hJ8fnXUQ7ZPL4PSUCu8QCCFaJCjMC1nv8DjCC6R9YX7tAzcWOv3z8 kz2Ci4elzQCm1oyhxKJKPAUoANtDPO2/8z2vNmWA01nMsz3ehWADpVto0WWHM2o1 ZCE+Mihx20rSL0c3P1IMWqoXdEllo3E10Tl/d1I1tPY0DQ/t6BjTSUnmbto41rGH at/sarpg4sznuA1eU+wbJbF0/3kAmK8GRdelGLjsVeq0EWIc5QfU7TAl+majz5cB Ep8Lh8gNAgMBAAECggEAajhZbdY/8vK1nSJbDN0aJJCb0sJr7mup+wmRLM8hLhZi +mV0mzYraq1gZA052SW8ZN2/klqbEYpA4w1H+5nfLUXkn8qKc4kUWIKkGPqSMdis P64Jf39i2FIbVQhdxgQAw+LioAxX4SFLTxCGUfQe8uUXPNrHktZF/f+ZcDbTXaMm 8Y2FyUBXBXuiDgdFw1cP4ShkMY6bGje1pAJ1gVMDKvGumL5L7XYQBF4idu+oUJvH xgZGbxihMA/MpSQK3qp+0/TjvQ3hyxPnoFaZ2IVWDhsdaTINJ88odBeWx/apYUhJ ZArs29e08h+CCDdm2ahgAysFOvRV9QsMrOz/D96LOQKBgQDldojO+OY6ApL+83D6 dtvPYUd0FZbgeNmmuNmpKvD73u2Ui2GfsJvp4DCyegCrxqMrvNVSCmJDUaYZr0qp M2Osbqksn+g0+SRGxSH8l0HhXJDiDCfIeWIWpma4MCnaMJyDq7Qi53gGG1ErXVC3 YjwhjFS8e7sHO+vrI3J3XnsVOwKBgQDg0E+3Jozfuv9AHUqYGfNg4UOs8kADbVTM uNEBQiEGLGvmXfJj5nwPv5IXlybhCf3pezEjGdosRoFkNgauQ2/L7LokWG6siJaE 3xRzWmHu6U7LNoIRc8kPTqf66tTtu9TJExI5uOVMWLq7KVS72qnlHbneq+kjbjmm JSNz5J2jVwKBgQCy97eOjiyqtBVISkEk6I1aesoLLUeG/lrroSMKwVZBbEcq42cZ 8No6GESC/4sEbyIW2+oZWcX4MXd2cvStcUpdU9YY2wN2RZdYpypx4ttcVSEfXVGu F5Y8ij51jAMojV+Vhtcxng1L3gR56QcqcLDrjZMNiwd9hevkcro1hfhDvwKBgDOq 7Ic1Tu8kdQFxOfGXFT5Qx1L6IggnmnOqji5x2lEm6G17bffTwvODnbnaPU8/EqIU dAiTKnc+hQJZAFQQn6MIdwdfY6A3jBBhjLuuLA/Sgw9lKaOFLtJby3N5gRJaNt83 iNrHSbuwMMpasweffsd23Cp67Av+izVKF8nM4wXlAoGBAMFoEH4QDsU9sCZ/7L9t ZstQJ6zPo/aEyVmVH8aogSmlVGBXTigIfXi33UbTqg93IfVGfL1AS+9Ey8I4jq/w 3RtEqe5jzFTdYakjQns++dMq4+0uLSm8XvEGzOZO6dv+dDHXjr3BXUqVFwyyta0O ERqSBDvaSh5zPEc0VeNrZ4Dp -----END PRIVATE KEY----- </key> key-direction 1 <tls-auth> -----BEGIN OpenVPN Static key V1----- 2c5942c3e9d2bf3ba6841c4dc83ac75b 9d73d8e18c45cfecfb98b6d111223d46 6e7eb7309e891e0966914c479e7db614 e847ebcc1f7364c9b4d12db64915e6e7 62cee3c02bbd11a467bbf3053598e865 bcc4497128d4b14816edf37a16737a58 e0f51f0309863ed6458e68730edfe8de 74e54c593b7278581cb3be0a100b2cf4 dae3e72c521a06a7b3ce2777bb7e0caa 42b4255b5dd05d4d5f0315f3989952fd 06a7acc06209a78fe23841818a02303e 2afe2b70cecc110d18bb8fdcb891fa76 7afc99574047c707e5df5afcba937403 4388a0f8ebfbff63079bf6fae3535c56 88f7d75982d56bc24e4e1ae51286c992 f81b01a21523656458941f19e3a98629 -----END OpenVPN Static key V1----- </tls-auth>
OpenVPN-配置文件 1. Openvpn Server 端配置文件################################################# # Sample OpenVPN 2.0 config file for # # multi-client server. # # # # This file is for the server side # # of a many-clients <-> one-server # # OpenVPN configuration. # # # # OpenVPN also supports # # single-machine <-> single-machine # # configurations (See the Examples page # # on the web site for more info). # # # # This config should work on Windows # # or Linux/BSD systems. Remember on # # Windows to quote pathnames and use # # double backslashes, e.g.: # # "C:\\Program Files\\OpenVPN\\config\\foo.key" # # # # Comments are preceded with '#' or ';' # ################################################# # Which local IP address should OpenVPN # listen on? (optional) ;local a.b.c.d # Which TCP/UDP port should OpenVPN listen on? # If you want to run multiple OpenVPN instances # on the same machine, use a different port # number for each one. You will need to # open up this port on your firewall. port 1194 # TCP or UDP server? proto tcp ;proto udp # "dev tun" will create a routed IP tunnel, # "dev tap" will create an ethernet tunnel. # Use "dev tap0" if you are ethernet bridging # and have precreated a tap0 virtual interface # and bridged it with your ethernet interface. # If you want to control access policies # over the VPN, you must create firewall # rules for the the TUN/TAP interface. # On non-Windows systems, you can give # an explicit unit number, such as tun0. # On Windows, use "dev-node" for this. # On most systems, the VPN will not function # unless you partially or fully disable # the firewall for the TUN/TAP interface. ;dev tap dev tun # Windows needs the TAP-Win32 adapter name # from the Network Connections panel if you # have more than one. On XP SP2 or higher, # you may need to selectively disable the # Windows firewall for the TAP adapter. # Non-Windows systems usually don't need this. ;dev-node MyTap # SSL/TLS root certificate (ca), certificate # (cert), and private key (key). Each client # and the server must have their own cert and # key file. The server and all clients will # use the same ca file. # # See the "easy-rsa" directory for a series # of scripts for generating RSA certificates # and private keys. Remember to use # a unique Common Name for the server # and each of the client certificates. # # Any X509 key management system can be used. # OpenVPN can also use a PKCS #12 formatted key file # (see "pkcs12" directive in man page). ca /etc/openvpn/certs/ca.crt cert /etc/openvpn/certs/server.crt key /etc/openvpn/certs/server.key # This file should be kept secret # Diffie hellman parameters. # Generate your own with: # openssl dhparam -out dh2048.pem 2048 #dh dh2048.pem dh /etc/openvpn/certs/dh.pem # Network topology # Should be subnet (addressing via IP) # unless Windows clients v2.0.9 and lower have to # be supported (then net30, i.e. a /30 per client) # Defaults to net30 (not recommended) ;topology subnet # Configure server mode and supply a VPN subnet # for OpenVPN to draw client addresses from. # The server will take 10.8.0.1 for itself, # the rest will be made available to clients. # Each client will be able to reach the server # on 10.8.0.1. Comment this line out if you are # ethernet bridging. See the man page for more info. server 10.8.0.0 255.255.255.0 # Maintain a record of client <-> virtual IP address # associations in this file. If OpenVPN goes down or # is restarted, reconnecting clients can be assigned # the same virtual IP address from the pool that was # previously assigned. ifconfig-pool-persist /var/log/openvpn/ipp.txt # Configure server mode for ethernet bridging. # You must first use your OS's bridging capability # to bridge the TAP interface with the ethernet # NIC interface. Then you must manually set the # IP/netmask on the bridge interface, here we # assume 10.8.0.4/255.255.255.0. Finally we # must set aside an IP range in this subnet # (start=10.8.0.50 end=10.8.0.100) to allocate # to connecting clients. Leave this line commented # out unless you are ethernet bridging. ;server-bridge 10.8.0.4 255.255.255.0 10.8.0.50 10.8.0.100 # Configure server mode for ethernet bridging # using a DHCP-proxy, where clients talk # to the OpenVPN server-side DHCP server # to receive their IP address allocation # and DNS server addresses. You must first use # your OS's bridging capability to bridge the TAP # interface with the ethernet NIC interface. # Note: this mode only works on clients (such as # Windows), where the client-side TAP adapter is # bound to a DHCP client. ;server-bridge # Push routes to the client to allow it # to reach other private subnets behind # the server. Remember that these # private subnets will also need # to know to route the OpenVPN client # address pool (10.8.0.0/255.255.255.0) # back to the OpenVPN server. ;push "route 192.168.10.0 255.255.255.0" ;push "route 192.168.20.0 255.255.255.0" # To assign specific IP addresses to specific # clients or if a connecting client has a private # subnet behind it that should also have VPN access, # use the subdirectory "ccd" for client-specific # configuration files (see man page for more info). # EXAMPLE: Suppose the client # having the certificate common name "Thelonious" # also has a small subnet behind his connecting # machine, such as 192.168.40.128/255.255.255.248. # First, uncomment out these lines: ;client-config-dir ccd ;route 192.168.40.128 255.255.255.248 # Then create a file ccd/Thelonious with this line: # iroute 192.168.40.128 255.255.255.248 # This will allow Thelonious' private subnet to # access the VPN. This example will only work # if you are routing, not bridging, i.e. you are # using "dev tun" and "server" directives. # EXAMPLE: Suppose you want to give # Thelonious a fixed VPN IP address of 10.9.0.1. # First uncomment out these lines: ;client-config-dir ccd ;route 10.9.0.0 255.255.255.252 # Then add this line to ccd/Thelonious: # ifconfig-push 10.9.0.1 10.9.0.2 # Suppose that you want to enable different # firewall access policies for different groups # of clients. There are two methods: # (1) Run multiple OpenVPN daemons, one for each # group, and firewall the TUN/TAP interface # for each group/daemon appropriately. # (2) (Advanced) Create a script to dynamically # modify the firewall in response to access # from different clients. See man # page for more info on learn-address script. ;learn-address ./script # If enabled, this directive will configure # all clients to redirect their default # network gateway through the VPN, causing # all IP traffic such as web browsing and # and DNS lookups to go through the VPN # (The OpenVPN server machine may need to NAT # or bridge the TUN/TAP interface to the internet # in order for this to work properly). ;push "redirect-gateway def1 bypass-dhcp" push "redirect-gateway def1" # Certain Windows-specific network settings # can be pushed to clients, such as DNS # or WINS server addresses. CAVEAT: # http://openvpn.net/faq.html#dhcpcaveats # The addresses below refer to the public # DNS servers provided by opendns.com. ;push "dhcp-option DNS 208.67.222.222" ;push "dhcp-option DNS 208.67.220.220" push "dhcp-option DNS 8.8.8.8" push "dhcp-option DNS 8.8.8.4" # Uncomment this directive to allow different # clients to be able to "see" each other. # By default, clients will only see the server. # To force clients to only see the server, you # will also need to appropriately firewall the # server's TUN/TAP interface. client-to-client # Uncomment this directive if multiple clients # might connect with the same certificate/key # files or common names. This is recommended # only for testing purposes. For production use, # each client should have its own certificate/key # pair. # # IF YOU HAVE NOT GENERATED INDIVIDUAL # CERTIFICATE/KEY PAIRS FOR EACH CLIENT, # EACH HAVING ITS OWN UNIQUE "COMMON NAME", # UNCOMMENT THIS LINE OUT. ;duplicate-cn # The keepalive directive causes ping-like # messages to be sent back and forth over # the link so that each side knows when # the other side has gone down. # Ping every 10 seconds, assume that remote # peer is down if no ping received during # a 120 second time period. keepalive 10 120 # For extra security beyond that provided # by SSL/TLS, create an "HMAC firewall" # to help block DoS attacks and UDP port flooding. # # Generate with: # openvpn --genkey --secret ta.key # # The server and each client must have # a copy of this key. # The second parameter should be '0' # on the server and '1' on the clients. tls-auth /etc/openvpn/server/certs/ta.key 0 # This file is secret # Select a cryptographic cipher. # This config item must be copied to # the client config file as well. # Note that v2.4 client/server will automatically # negotiate AES-256-GCM in TLS mode. # See also the ncp-cipher option in the manpage cipher AES-256-CBC # Enable compression on the VPN link and push the # option to the client (v2.4+ only, for earlier # versions see below) ;compress lz4-v2 ;push "compress lz4-v2" # For compression compatible with older clients use comp-lzo # If you enable it here, you must also # enable it in the client config file. ;comp-lzo # The maximum number of concurrently connected # clients we want to allow. ;max-clients 100 # It's a good idea to reduce the OpenVPN # daemon's privileges after initialization. # # You can uncomment this out on # non-Windows systems. ;user nobody ;group nogroup # The persist options will try to avoid # accessing certain resources on restart # that may no longer be accessible because # of the privilege downgrade. persist-key persist-tun # Output a short status file showing # current connections, truncated # and rewritten every minute. status /var/log/openvpn/openvpn-status.log # By default, log messages will go to the syslog (or # on Windows, if running as a service, they will go to # the "\Program Files\OpenVPN\log" directory). # Use log or log-append to override this default. # "log" will truncate the log file on OpenVPN startup, # while "log-append" will append to it. Use one # or the other (but not both). ;log /var/log/openvpn/openvpn.log ;log-append /var/log/openvpn/openvpn.log # Set the appropriate level of log # file verbosity. # # 0 is silent, except for fatal errors # 4 is reasonable for general usage # 5 and 6 can help to debug connection problems # 9 is extremely verbose verb 3 # Silence repeating messages. At most 20 # sequential messages of the same message # category will be output to the log. ;mute 20 # Notify the client that when the server restarts so it # can automatically reconnect. explicit-exit-notify 0 crl-verify /etc/openvpn/easyrsa/pki/crl.pem1. Openvpn Client 端配置文件############################################## # Sample client-side OpenVPN 2.0 config file # # for connecting to multi-client server. # # # # This configuration can be used by multiple # # clients, however each client should have # # its own cert and key files. # # # # On Windows, you might want to rename this # # file so it has a .ovpn extension # ############################################## # Specify that we are a client and that we # will be pulling certain config file directives # from the server. client # Use the same setting as you are using on # the server. # On most systems, the VPN will not function # unless you partially or fully disable # the firewall for the TUN/TAP interface. ;dev tap dev tun # Windows needs the TAP-Win32 adapter name # from the Network Connections panel # if you have more than one. On XP SP2, # you may need to disable the firewall # for the TAP adapter. ;dev-node MyTap # Are we connecting to a TCP or # UDP server? Use the same setting as # on the server. proto tcp ;proto udp # The hostname/IP and port of the server. # You can have multiple remote entries # to load balance between the servers. remote my-server-1 1194 ;remote my-server-2 1194 # Choose a random host from the remote # list for load-balancing. Otherwise # try hosts in the order specified. ;remote-random # Keep trying indefinitely to resolve the # host name of the OpenVPN server. Very useful # on machines which are not permanently connected # to the internet such as laptops. resolv-retry infinite # Most clients don't need to bind to # a specific local port number. nobind # Downgrade privileges after initialization (non-Windows only) ;user nobody ;group nogroup # Try to preserve some state across restarts. persist-key persist-tun # If you are connecting through an # HTTP proxy to reach the actual OpenVPN # server, put the proxy server/IP and # port number here. See the man page # if your proxy server requires # authentication. ;http-proxy-retry # retry on connection failures ;http-proxy [proxy server] [proxy port #] # Wireless networks often produce a lot # of duplicate packets. Set this flag # to silence duplicate packet warnings. ;mute-replay-warnings # SSL/TLS parms. # See the server config file for more # description. It's best to use # a separate .crt/.key file pair # for each client. A single ca # file can be used for all clients. ca ca.crt cert username.crt key username.key # Verify server certificate by checking that the # certicate has the correct key usage set. # This is an important precaution to protect against # a potential attack discussed here: # http://openvpn.net/howto.html#mitm # # To use this feature, you will need to generate # your server certificates with the keyUsage set to # digitalSignature, keyEncipherment # and the extendedKeyUsage to # serverAuth # EasyRSA can do this for you. remote-cert-tls server # If a tls-auth key is used on the server # then every client must also have the key. tls-auth ta.key 1 # Select a cryptographic cipher. # If the cipher option is used on the server # then you must also specify it here. # Note that v2.4 client/server will automatically # negotiate AES-256-GCM in TLS mode. # See also the ncp-cipher option in the manpage cipher AES-256-CBC # Enable compression on the VPN link. # Don't enable this unless it is also # enabled in the server config file. #comp-lzo # Set log file verbosity. verb 3 # Silence repeating messages ;mute 203. Openvpn APP 配置[Tips] IOS客户端配置client dev tun ;proto tcp proto udp remote xxx.xxx.xxx.xxx 1194 resolv-retry infinite nobind persist-key persist-tun mute-replay-warnings #ca ca.crt #cert client02.crt #key client02.key remote-cert-tls server #tls-auth ta.key 1 #comp-lzo verb 3 <ca> -----BEGIN CERTIFICATE----- MIIDJDCCAgygAwIBAgIJAMv+3UPUdlJjMA0GCSqGSIb3DQEBCwUAMBExDzANBgNV BAMMBnNlcnZlcjAeFw0yMjA0MjEwOTEzNDJaFw0zMjA0MTgwOTEzNDJaMBExDzAN BgNVBAMMBnNlcnZlcjCCASIwDQYJKoZIhvcNAQEBBQADggEPADCCAQoCggEBAJ3n HQJcnsmqkPJwLEV8YymrH1l7189/sXmJ0sa5mIYIcBKKL5haAQ6rdjRlJtuTDnoA oFJ1+Uf9Qwpxs/Tj4blsfewsSD5WlXGq2htgXZv8jjIiKwpSjN2LImJi0pOuow/v nFYGA58Xtsg4EDCIGF5LWc8L0WdfmkvN+LFvUQtnlzyIJ1haHFJdCNtgxpj8Khsa GDDRX7Nr4abnTAQwEb6jcReAhvrqu/b5CtgQDYBHV6pY1toXwZ8PzFnay4ngQFJA 5KUoFsso4beHl/F7u4O44CH61rJwiPavRKBwbYZt6ySU7mQkJRC1yQkRNV4HKwdB 6DOBdmZ+CDJSfMbkpysCAwEAAaN/MH0wHQYDVR0OBBYEFLcvJFbXdouS61U7FQ+d OTmjS20JMEEGA1UdIwQ6MDiAFLcvJFbXdouS61U7FQ+dOTmjS20JoRWkEzARMQ8w DQYDVQQDDAZzZXJ2ZXKCCQDL/t1D1HZSYzAMBgNVHRMEBTADAQH/MAsGA1UdDwQE AwIBBjANBgkqhkiG9w0BAQsFAAOCAQEAQt6Qxbp2sNc/WtRY7jhLl7J52kMzpoO/ 5MWmqoHZ4IU1yM9hN3KzJIby0d0JgzlWAPvl74RnV3Padu5xSlYeCK8y+EOKuJXx b/CXPloHET5EcGLpZWnhFzTUrG68QUAeP3mwP+rr+2/RTSoYNq8Qu5r8npHjhr40 xH+dLtBZDAOLJcKgi4lgCu8WINCMgPwDd5hAsGD1ul7Lso3xGlHJePt6pV2tM45e BD8vhF59WpShIRYlLqWbRG9glB7IFws024jefCEThSXuPt5M6cSO15pqDkeSjG25 CNtvgMw+VSFeBzvs2hEgY8x08pU2EPn1lhmfolcmRVdg8i0qnJBpRg== -----END CERTIFICATE----- </ca> <cert> -----BEGIN CERTIFICATE----- MIIDQjCCAiqgAwIBAgIRANLIdjgXLZIM++/mhxiBLRYwDQYJKoZIhvcNAQELBQAw ETEPMA0GA1UEAwwGc2VydmVyMB4XDTIyMDQyMTEyNTEwOVoXDTI0MDcyNDEyNTEw OVowEzERMA8GA1UEAwwIY2xpZW50MDIwggEiMA0GCSqGSIb3DQEBAQUAA4IBDwAw ggEKAoIBAQDJgm94AHU2P8NpTTuPIDLCQxT3fqJafi/67Yy2LgTAbif+C/9aUuXC M/wJ4fUcBej82+oga583wfwSECubxAaiJc6hJ8fnXUQ7ZPL4PSUCu8QCCFaJCjMC 1nv8DjCC6R9YX7tAzcWOv3z8kz2Ci4elzQCm1oyhxKJKPAUoANtDPO2/8z2vNmWA 01nMsz3ehWADpVto0WWHM2o1ZCE+Mihx20rSL0c3P1IMWqoXdEllo3E10Tl/d1I1 tPY0DQ/t6BjTSUnmbto41rGHat/sarpg4sznuA1eU+wbJbF0/3kAmK8GRdelGLjs Veq0EWIc5QfU7TAl+majz5cBEp8Lh8gNAgMBAAGjgZIwgY8wCQYDVR0TBAIwADAd BgNVHQ4EFgQUUgrZwhdjvyyLaMdexvU32gKz/+4wQQYDVR0jBDowOIAUty8kVtd2 i5LrVTsVD505OaNLbQmhFaQTMBExDzANBgNVBAMMBnNlcnZlcoIJAMv+3UPUdlJj MBMGA1UdJQQMMAoGCCsGAQUFBwMCMAsGA1UdDwQEAwIHgDANBgkqhkiG9w0BAQsF AAOCAQEAl07HOolF0Hos9oHfcQlztWt+WNHKQBQ/FxVjufwYv8cZRu+eZozrZvZe fA4mgzvPXsDRZlLKqL4zLhsGyEUTcjAdvhh0s7PVqgppWN1pLEozTvhgJ8r8L8ev fRXf7R0bJHPzzqFdBzdnFhZ3D4fnDafEFlXfqpl30TdEP50CRjYHk1U+0PWyl3+l 05SBCvNaF0nrK+gD2VDtIHp17nB6LFdpW03sBmkLCVy9KDhk1Z0zwtoJe8RI98sj 2r/7ApuXh6otEJlaFKZ0ChotJL4QEBM5nVOJNFWCvu34KXJevkhRQYTwlKsjgfDN eDOvxAOxozI1HegVavrl8K70iFUhQw== -----END CERTIFICATE----- </cert> <key> -----BEGIN PRIVATE KEY----- MIIEvgIBADANBgkqhkiG9w0BAQEFAASCBKgwggSkAgEAAoIBAQDJgm94AHU2P8Np TTuPIDLCQxT3fqJafi/67Yy2LgTAbif+C/9aUuXCM/wJ4fUcBej82+ogDwnyIzPe IrubxAaiJc6hJ8fnXUQ7ZPL4PSUCu8QCCFaJCjMC1nv8DjCC6R9YX7tAzcWOv3z8 kz2Ci4elzQCm1oyhxKJKPAUoANtDPO2/8z2vNmWA01nMsz3ehWADpVto0WWHM2o1 ZCE+Mihx20rSL0c3P1IMWqoXdEllo3E10Tl/d1I1tPY0DQ/t6BjTSUnmbto41rGH at/sarpg4sznuA1eU+wbJbF0/3kAmK8GRdelGLjsVeq0EWIc5QfU7TAl+majz5cB Ep8Lh8gNAgMBAAECggEAajhZbdY/8vK1nSJbDN0aJJCb0sJr7mup+wmRLM8hLhZi +mV0mzYraq1gZA052SW8ZN2/klqbEYpA4w1H+5nfLUXkn8qKc4kUWIKkGPqSMdis P64Jf39i2FIbVQhdxgQAw+LioAxX4SFLTxCGUfQe8uUXPNrHktZF/f+ZcDbTXaMm 8Y2FyUBXBXuiDgdFw1cP4ShkMY6bGje1pAJ1gVMDKvGumL5L7XYQBF4idu+oUJvH xgZGbxihMA/MpSQK3qp+0/TjvQ3hyxPnoFaZ2IVWDhsdaTINJ88odBeWx/apYUhJ ZArs29e08h+CCDdm2ahgAysFOvRV9QsMrOz/D96LOQKBgQDldojO+OY6ApL+83D6 dtvPYUd0FZbgeNmmuNmpKvD73u2Ui2GfsJvp4DCyegCrxqMrvNVSCmJDUaYZr0qp M2Osbqksn+g0+SRGxSH8l0HhXJDiDCfIeWIWpma4MCnaMJyDq7Qi53gGG1ErXVC3 YjwhjFS8e7sHO+vrI3J3XnsVOwKBgQDg0E+3Jozfuv9AHUqYGfNg4UOs8kADbVTM uNEBQiEGLGvmXfJj5nwPv5IXlybhCf3pezEjGdosRoFkNgauQ2/L7LokWG6siJaE 3xRzWmHu6U7LNoIRc8kPTqf66tTtu9TJExI5uOVMWLq7KVS72qnlHbneq+kjbjmm JSNz5J2jVwKBgQCy97eOjiyqtBVISkEk6I1aesoLLUeG/lrroSMKwVZBbEcq42cZ 8No6GESC/4sEbyIW2+oZWcX4MXd2cvStcUpdU9YY2wN2RZdYpypx4ttcVSEfXVGu F5Y8ij51jAMojV+Vhtcxng1L3gR56QcqcLDrjZMNiwd9hevkcro1hfhDvwKBgDOq 7Ic1Tu8kdQFxOfGXFT5Qx1L6IggnmnOqji5x2lEm6G17bffTwvODnbnaPU8/EqIU dAiTKnc+hQJZAFQQn6MIdwdfY6A3jBBhjLuuLA/Sgw9lKaOFLtJby3N5gRJaNt83 iNrHSbuwMMpasweffsd23Cp67Av+izVKF8nM4wXlAoGBAMFoEH4QDsU9sCZ/7L9t ZstQJ6zPo/aEyVmVH8aogSmlVGBXTigIfXi33UbTqg93IfVGfL1AS+9Ey8I4jq/w 3RtEqe5jzFTdYakjQns++dMq4+0uLSm8XvEGzOZO6dv+dDHXjr3BXUqVFwyyta0O ERqSBDvaSh5zPEc0VeNrZ4Dp -----END PRIVATE KEY----- </key> key-direction 1 <tls-auth> -----BEGIN OpenVPN Static key V1----- 2c5942c3e9d2bf3ba6841c4dc83ac75b 9d73d8e18c45cfecfb98b6d111223d46 6e7eb7309e891e0966914c479e7db614 e847ebcc1f7364c9b4d12db64915e6e7 62cee3c02bbd11a467bbf3053598e865 bcc4497128d4b14816edf37a16737a58 e0f51f0309863ed6458e68730edfe8de 74e54c593b7278581cb3be0a100b2cf4 dae3e72c521a06a7b3ce2777bb7e0caa 42b4255b5dd05d4d5f0315f3989952fd 06a7acc06209a78fe23841818a02303e 2afe2b70cecc110d18bb8fdcb891fa76 7afc99574047c707e5df5afcba937403 4388a0f8ebfbff63079bf6fae3535c56 88f7d75982d56bc24e4e1ae51286c992 f81b01a21523656458941f19e3a98629 -----END OpenVPN Static key V1----- </tls-auth> -
 Typeperf From: TypeperfTypeperf 参数:C:\>typeperf /? Microsoft ® TypePerf.exe (6.1.7601.18869)Typeperf 将性能数据写入命令窗口或日志文件。要停止 Typeperf,请按 CTRL+C.用法:typeperf { <counter [counter ...]> | -cf <filename> | -q [object] | -qx [object] } [options]参数: <counter [counter ...]> 要监视的性能计数器。选项说明-?显示跟上下文相关的帮助。-f <CSV/TSV/BIN/SQL>输出文件格式。默认值是 CSV。-cf 含有监视的性能计数器的文件,一个计数器一行。-si <[[hh:]mm:]ss>示例间的时间。默认值是 1 秒。-o 输出文件或 SQL 数据库的路径。默认值为 STDOUT。-q [object]列出已安装的计数器(无实例)。要列出某个对象的计数器,包括对象名, 如 Processor。-qx [object]列出已安装的计数器(带实例)。要列出某个对象的计数器,包括对象名, 如 Processor。-sc 要收集的示例数量。默认值为,在 CTRL+C 之前都进行采样。-config 含有命令选项的设置文件。-s <computer_name>在计数器路径中没有指定服务器的情况下要监视的服务器。-y不用提示对所有问题都回答 yes。注意: Counter 是性能计数器的全名,格式为 "\\<Computer>\<Object>(<Instance>)\<Counter>"; 例如 "\\Server1\Processor(0)\% User Time"。示例: typeperf "\Processor(_Total)\% Processor Time" typeperf -cf counters.txt -si 5 -sc 50 -f TSV -o domain2.tsv typeperf -qx PhysicalDisk -o counters.txt
Typeperf From: TypeperfTypeperf 参数:C:\>typeperf /? Microsoft ® TypePerf.exe (6.1.7601.18869)Typeperf 将性能数据写入命令窗口或日志文件。要停止 Typeperf,请按 CTRL+C.用法:typeperf { <counter [counter ...]> | -cf <filename> | -q [object] | -qx [object] } [options]参数: <counter [counter ...]> 要监视的性能计数器。选项说明-?显示跟上下文相关的帮助。-f <CSV/TSV/BIN/SQL>输出文件格式。默认值是 CSV。-cf 含有监视的性能计数器的文件,一个计数器一行。-si <[[hh:]mm:]ss>示例间的时间。默认值是 1 秒。-o 输出文件或 SQL 数据库的路径。默认值为 STDOUT。-q [object]列出已安装的计数器(无实例)。要列出某个对象的计数器,包括对象名, 如 Processor。-qx [object]列出已安装的计数器(带实例)。要列出某个对象的计数器,包括对象名, 如 Processor。-sc 要收集的示例数量。默认值为,在 CTRL+C 之前都进行采样。-config 含有命令选项的设置文件。-s <computer_name>在计数器路径中没有指定服务器的情况下要监视的服务器。-y不用提示对所有问题都回答 yes。注意: Counter 是性能计数器的全名,格式为 "\\<Computer>\<Object>(<Instance>)\<Counter>"; 例如 "\\Server1\Processor(0)\% User Time"。示例: typeperf "\Processor(_Total)\% Processor Time" typeperf -cf counters.txt -si 5 -sc 50 -f TSV -o domain2.tsv typeperf -qx PhysicalDisk -o counters.txt -
 深信服AF &锐捷 OID表 一、深信服AF OID1. 找出要监控项目的SNMP字符串(或OID)。要获取SNMP字符串列表,请使用 snmpwalk 命令(net-snmp的部分软件应该在Zabbix安装时同时安装)或等效工具:shell> snmpwalk -v 2c -c public <host IP> .这里的'2c'代表SNMP版本,你也可以将其替换为'1',以在设备上指定SNMP版本为v1。它会返回给你一个SNMP字符串及其最后一个值的列表。如果不是,那么SNMP 'community' 可能与标准的'public'不同,在这种情况下,请找出它是什么。然后,你可以浏览列表,直到找到要监控的字符串,例如:如果要监视通过端口3进入交换机的字节,你将使用此行中的IF-MIB :: ifInOctets.3字符串:IF-MIB::ifInOctets.3 = Counter32: 3409739121你现在可以使用 snmpget 命令找出'IF-MIB :: ifInOctets.3'的数字OID:shell> snmpget -v 2c -c public -On 10.62.1.22 IF-MIB::ifInOctets.3请注意,字符串中的最后一个数字是你要监控的端口号。请参考: 动态索引.如下所示:.1.3.6.1.2.1.2.2.1.10.3 = Counter32: 3472126941重复一遍,OID中的最后一个号码是端口号。3COM似乎是使用数百个端口号,例如 端口1=端口101,端口3=端口103,但思科使用常规数字,例如。 端口3=3。一些最常用的SNMP OID,Zabbix将自动转换为数字表示。在上面的例子中,值类型是“Counter32”它在内部对应于ASN_COUNTER类型。完整的支持类型包括 ASN_COUNTER, ASN_COUNTER64, ASN_UINTEGER, ASN_UNSIGNED64, ASN_INTEGER, ASN_INTEGER64, ASN_FLOAT, ASN_DOUBLE, ASN_TIMETICKS, ASN_GAUGE, ASN_IPADDRESS, ASN_OCTET_STR 和 ASN_OBJECT_ID (从2.2.8, 2.4.3之后). 这些类型大致对应于snmpget 输出的 "Counter32", "Counter64", "UInteger32", "INTEGER", "Float", "Double", "Timeticks", "Gauge32", "IpAddress", "OCTET STRING", "OBJECT IDENTIFIER", 但也有可能显示为 "STRING", "Hex-STRING", "OID" 或者其它, 这取这取决于显示提示的表达方式。MIBDescriptionOIDSNMPv2-MIB::sysDescr.0系统描述.1.3.6.1.2.1.1.1.0SNMPv2-MIB::sysContact.0联系.1.3.6.1.2.1.1.4.0SNMPv2-MIB::sysName.0系统名.1.3.6.1.2.1.1.5.0SNMPv2-MIB::sysLocation.0位置.1.3.6.1.2.1.1.6.0SNMPv2-MIB::sysServices.0系统服务.1.3.6.1.2.1.1.7.0SNMPv2-MIB::sysConnNum.0连接数.1.3.6.1.2.1.1.10.0SNMPv2-MIB::sysCpuUsage.0cpu占用率.1.3.6.1.2.1.1.11.0SNMPv2-MIB::sysMemUsage.0内存占用率.1.3.6.1.2.1.1.12.0SNMPv2-MIB::sysDiskUsage.0磁盘占用率.1.3.6.1.2.1.1.13.0HOST-RESOURCES-MIB::hrSystemDate.0系统日期.1.3.6.1.2.1.25.1.2.0HOST-RESOURCES-MIB::hrSystemUptime.0运行的时间.1.3.6.1.2.1.25.1.1.0SNMPv2-MIB::sysDescrFull.0系统信息.1.3.6.1.2.1.1.15.0系统信息NameDescriptionOIDhrSystemUptime运行的时间.1.3.6.1.2.1.25.1.1hrSystemDate系统日期.1.3.6.1.2.1.25.1.2hrSystemNumUsers用户数.1.3.6.1.2.1.25.1.5hrSystemProcesses进程数.1.3.6.1.2.1.25.1.6hrSystemMaxProcesses最大进程数.1.3.6.1.2.1.25.1.7HOST-RESOURCES-MIB::hrMemorySize.0系统内存.1.3.6.1.2.1.25.2.2hrStorageTable存储设备信息表(内存,磁盘的使用情况).1.3.6.1.2.1.25.2.3hrDeviceTable系统设备列表.1.3.6.1.2.1.25.3.2hrSWRunTable系统进程列表.1.3.6.1.2.1.25.4.2CPUNameDescriptionOIDUCD-SNMP-MIB::ssCpuUser用户使用CPU情况.1.3.6.1.4.1.2021.11.9.0UCD-SNMP-MIB::ssCpuSystem.0系统使用CPU情况.1.3.6.1.4.1.2021.11.10.0UCD-SNMP-MIB::ssCpuIdle.0空闲CPU.1.3.6.1.4.1.2021.11.11.0SNMPv2-MIB::sysCpuUsage.0cpu占用率.1.3.6.1.2.1.1.11.0内存NameDescriptionOIDmemTotalSwap总swap分区.1.3.6.1.4.1.2021.4.3memAvailSwap可用swap分区.1.3.6.1.4.1.2021.4.4memTotalReal内存总量(真实内存).1.3.6.1.4.1.2021.4.5memAvailReal可用内存(真实内存).1.3.6.1.4.1.2021.4.6memTotalFree可用内存(真实内存+虚拟内存).1.3.6.1.4.1.2021.4.11memShared共享内存数量.1.3.6.1.4.1.2021.4.13memBufferbuffer内存数量.1.3.6.1.4.1.2021.4.14memCachedCache内存数量.1.3.6.1.4.1.2021.4.15hrMemorySize内存总量.1.3.6.1.2.1.25.2.2hrStorageTable存储设备信息表(内存,磁盘).1.3.6.1.2.1.25.2.3硬盘NameDescriptionOIDsysDiskUsage磁盘占用率.1.3.6.1.2.1.1.13hrStorageTable存储设备信息表(内存,磁盘).1.3.6.1.2.1.25.2.3网口NameDescriptionOIDifNumber接口总数.1.3.6.1.2.1.2.1ifTable接口表(接口名,开启状态,MAC,出口流量,入口流量等).1.3.6.1.2.1.2.2ifIndex索引.1.3.6.1.2.1.2.2.1.1ifName网口.1.3.6.1.2.1.2.2.1.2ifType接口类型.1.3.6.1.2.1.2.2.1.3ifMtu接口MTU.1.3.6.1.2.1.2.2.1.4ifPhysAddress接口mac地址.1.3.6.1.2.1.2.2.1.6ifAdminStatus所希望的接口工作状态.1.3.6.1.2.1.2.2.1.7ifOperStatus当前接口工作状态.1.3.6.1.2.1.2.2.1.8ifInOctets接口收到的字节总数.1.3.6.1.2.1.2.2.1.10ifOutOctets接口发送的字节总数.1.3.6.1.2.1.2.2.1.16地址转换表NameDescriptionOIDatTable地址转换表.1.3.6.1.2.1.3.1IPNameDescriptionOIDipForwarding是否作为一个IP网关.1.3.6.1.2.1.4.1ipDefaultTTLIP头中的Time To Live字段的值.1.3.6.1.2.1.4.2ipInReceivesIP层从下层接收的数据报总数.1.3.6.1.2.1.4.3ipInHdrErrors由于IP头出错而丢弃的数据报.1.3.6.1.2.1.4.4ipInAddrErrors地址出错(无效地址、不支持的地址和非本地主机地址)的数据报.1.3.6.1.2.1.4.5ipForwDatagrams已转发的数据报.1.3.6.1.2.1.4.6ipInUnknownProtos不支持数据报的协议,因而被丢弃.1.3.6.1.2.1.4.7ipInDiscards因缺乏缓冲资源而丢弃的数据报.1.3.6.1.2.1.4.8ipInDelivers由IP层提交给上层的数据报.1.3.6.1.2.1.4.9ipOutRequests由IP层交给下层需要发送的数据报,不包括ipForwDatagrams.1.3.6.1.2.1.4.10ipOutDiscards在输出端因缺乏缓冲资源而丢弃的数据报.1.3.6.1.2.1.4.11ipOutNoRoutes没有到达目标的路由而丢弃的数据报.1.3.6.1.2.1.4.12ipReasmTimeout数据段等待重装配的最长时间(秒).1.3.6.1.2.1.4.13ipReasmReqds需要重装配的数据段.1.3.6.1.2.1.4.14ipReasmOKs成功重装配的数据段.1.3.6.1.2.1.4.15ipReasmFails不能重装配的数据段.1.3.6.1.2.1.4.16ipFragOKs分段成功的数据段.1.3.6.1.2.1.4.17ipFragFails不能分段的数据段.1.3.6.1.2.1.4.18ipFragCreates产生的数据报分段数.1.3.6.1.2.1.4.19ipAddrTableIP地址表.1.3.6.1.2.1.4.20ipRouteTableIP路由表.1.3.6.1.2.1.4.21ipNetToMediaTableIP与物理地址转换表.1.3.6.1.2.1.4.22ipRoutingDiscards无效的路由项,包括为释放缓冲空间而丢弃路由项.1.3.6.1.2.1.4.23TCPNameDescriptionOIDtcpRtoAlgorithm重传时间算法.1.3.6.1.2.1.6.1tcpRtoMin重传时间最小值.1.3.6.1.2.1.6.2tcpRtoMax重传时间最大值.1.3.6.1.2.1.6.3tcpMaxConn可建立的最大连接数.1.3.6.1.2.1.6.4tcpActiveOpens主动打开的连接数.1.3.6.1.2.1.6.5tcpPassiveOpens被动打开的连接数.1.3.6.1.2.1.6.6tcpAttemptFails连接建立失败数.1.3.6.1.2.1.6.7tcpEstabResets连接复位数.1.3.6.1.2.1.6.8tcpCurrEstab状态为established或closeWait的连接数.1.3.6.1.2.1.6.9tcpInSegs接收的TCP段总数.1.3.6.1.2.1.6.10tcpOutSegs发送的TCP段总数.1.3.6.1.2.1.6.11tcpRetransSegs重传的TCP段总数.1.3.6.1.2.1.6.12tcpConnTable连接表.1.3.6.1.2.1.6.13tcpInErrors接收的出错TCP段数.1.3.6.1.2.1.6.14tcpOutRests发出的含RST标志的段数.1.3.6.1.2.1.6.15UDPName Description OIDudpInDatagrams 接收的数据报总数 .1.3.6.1.2.1.7.1udpNoPorts 没有发现端口而无法提交的数据报 .1.3.6.1.2.1.7.2udpInErrors 出错的数据报 .1.3.6.1.2.1.7.3udpOutDatagrams 上层协议要求输出的数据报 .1.3.6.1.2.1.7.4udpTable UDP表 .1.3.6.1.2.1.7.5SNMPNameDescriptionOIDsnmpInPktsSNMP模块接收到的分组数.1.3.6.1.2.1.11.1snmpInTotalReqVars被成功读取的Object数,包括get-request和get-next操作.1.3.6.1.2.1.11.13snmpInGetRequestsSNMP模块接收到并处理的get-request的分组数.1.3.6.1.2.1.11.15snmpInGetNextsSNMP模块接收到并处理的get-next的分组数.1.3.6.1.2.1.11.16snmpOutGetResponsesSNMP模块发出的get-responses的分组数.1.3.6.1.2.1.11.28snmpEnableAuthenTraps标记是否允许代理程序产生检验失败警告.1.3.6.1.2.1.11.30
深信服AF &锐捷 OID表 一、深信服AF OID1. 找出要监控项目的SNMP字符串(或OID)。要获取SNMP字符串列表,请使用 snmpwalk 命令(net-snmp的部分软件应该在Zabbix安装时同时安装)或等效工具:shell> snmpwalk -v 2c -c public <host IP> .这里的'2c'代表SNMP版本,你也可以将其替换为'1',以在设备上指定SNMP版本为v1。它会返回给你一个SNMP字符串及其最后一个值的列表。如果不是,那么SNMP 'community' 可能与标准的'public'不同,在这种情况下,请找出它是什么。然后,你可以浏览列表,直到找到要监控的字符串,例如:如果要监视通过端口3进入交换机的字节,你将使用此行中的IF-MIB :: ifInOctets.3字符串:IF-MIB::ifInOctets.3 = Counter32: 3409739121你现在可以使用 snmpget 命令找出'IF-MIB :: ifInOctets.3'的数字OID:shell> snmpget -v 2c -c public -On 10.62.1.22 IF-MIB::ifInOctets.3请注意,字符串中的最后一个数字是你要监控的端口号。请参考: 动态索引.如下所示:.1.3.6.1.2.1.2.2.1.10.3 = Counter32: 3472126941重复一遍,OID中的最后一个号码是端口号。3COM似乎是使用数百个端口号,例如 端口1=端口101,端口3=端口103,但思科使用常规数字,例如。 端口3=3。一些最常用的SNMP OID,Zabbix将自动转换为数字表示。在上面的例子中,值类型是“Counter32”它在内部对应于ASN_COUNTER类型。完整的支持类型包括 ASN_COUNTER, ASN_COUNTER64, ASN_UINTEGER, ASN_UNSIGNED64, ASN_INTEGER, ASN_INTEGER64, ASN_FLOAT, ASN_DOUBLE, ASN_TIMETICKS, ASN_GAUGE, ASN_IPADDRESS, ASN_OCTET_STR 和 ASN_OBJECT_ID (从2.2.8, 2.4.3之后). 这些类型大致对应于snmpget 输出的 "Counter32", "Counter64", "UInteger32", "INTEGER", "Float", "Double", "Timeticks", "Gauge32", "IpAddress", "OCTET STRING", "OBJECT IDENTIFIER", 但也有可能显示为 "STRING", "Hex-STRING", "OID" 或者其它, 这取这取决于显示提示的表达方式。MIBDescriptionOIDSNMPv2-MIB::sysDescr.0系统描述.1.3.6.1.2.1.1.1.0SNMPv2-MIB::sysContact.0联系.1.3.6.1.2.1.1.4.0SNMPv2-MIB::sysName.0系统名.1.3.6.1.2.1.1.5.0SNMPv2-MIB::sysLocation.0位置.1.3.6.1.2.1.1.6.0SNMPv2-MIB::sysServices.0系统服务.1.3.6.1.2.1.1.7.0SNMPv2-MIB::sysConnNum.0连接数.1.3.6.1.2.1.1.10.0SNMPv2-MIB::sysCpuUsage.0cpu占用率.1.3.6.1.2.1.1.11.0SNMPv2-MIB::sysMemUsage.0内存占用率.1.3.6.1.2.1.1.12.0SNMPv2-MIB::sysDiskUsage.0磁盘占用率.1.3.6.1.2.1.1.13.0HOST-RESOURCES-MIB::hrSystemDate.0系统日期.1.3.6.1.2.1.25.1.2.0HOST-RESOURCES-MIB::hrSystemUptime.0运行的时间.1.3.6.1.2.1.25.1.1.0SNMPv2-MIB::sysDescrFull.0系统信息.1.3.6.1.2.1.1.15.0系统信息NameDescriptionOIDhrSystemUptime运行的时间.1.3.6.1.2.1.25.1.1hrSystemDate系统日期.1.3.6.1.2.1.25.1.2hrSystemNumUsers用户数.1.3.6.1.2.1.25.1.5hrSystemProcesses进程数.1.3.6.1.2.1.25.1.6hrSystemMaxProcesses最大进程数.1.3.6.1.2.1.25.1.7HOST-RESOURCES-MIB::hrMemorySize.0系统内存.1.3.6.1.2.1.25.2.2hrStorageTable存储设备信息表(内存,磁盘的使用情况).1.3.6.1.2.1.25.2.3hrDeviceTable系统设备列表.1.3.6.1.2.1.25.3.2hrSWRunTable系统进程列表.1.3.6.1.2.1.25.4.2CPUNameDescriptionOIDUCD-SNMP-MIB::ssCpuUser用户使用CPU情况.1.3.6.1.4.1.2021.11.9.0UCD-SNMP-MIB::ssCpuSystem.0系统使用CPU情况.1.3.6.1.4.1.2021.11.10.0UCD-SNMP-MIB::ssCpuIdle.0空闲CPU.1.3.6.1.4.1.2021.11.11.0SNMPv2-MIB::sysCpuUsage.0cpu占用率.1.3.6.1.2.1.1.11.0内存NameDescriptionOIDmemTotalSwap总swap分区.1.3.6.1.4.1.2021.4.3memAvailSwap可用swap分区.1.3.6.1.4.1.2021.4.4memTotalReal内存总量(真实内存).1.3.6.1.4.1.2021.4.5memAvailReal可用内存(真实内存).1.3.6.1.4.1.2021.4.6memTotalFree可用内存(真实内存+虚拟内存).1.3.6.1.4.1.2021.4.11memShared共享内存数量.1.3.6.1.4.1.2021.4.13memBufferbuffer内存数量.1.3.6.1.4.1.2021.4.14memCachedCache内存数量.1.3.6.1.4.1.2021.4.15hrMemorySize内存总量.1.3.6.1.2.1.25.2.2hrStorageTable存储设备信息表(内存,磁盘).1.3.6.1.2.1.25.2.3硬盘NameDescriptionOIDsysDiskUsage磁盘占用率.1.3.6.1.2.1.1.13hrStorageTable存储设备信息表(内存,磁盘).1.3.6.1.2.1.25.2.3网口NameDescriptionOIDifNumber接口总数.1.3.6.1.2.1.2.1ifTable接口表(接口名,开启状态,MAC,出口流量,入口流量等).1.3.6.1.2.1.2.2ifIndex索引.1.3.6.1.2.1.2.2.1.1ifName网口.1.3.6.1.2.1.2.2.1.2ifType接口类型.1.3.6.1.2.1.2.2.1.3ifMtu接口MTU.1.3.6.1.2.1.2.2.1.4ifPhysAddress接口mac地址.1.3.6.1.2.1.2.2.1.6ifAdminStatus所希望的接口工作状态.1.3.6.1.2.1.2.2.1.7ifOperStatus当前接口工作状态.1.3.6.1.2.1.2.2.1.8ifInOctets接口收到的字节总数.1.3.6.1.2.1.2.2.1.10ifOutOctets接口发送的字节总数.1.3.6.1.2.1.2.2.1.16地址转换表NameDescriptionOIDatTable地址转换表.1.3.6.1.2.1.3.1IPNameDescriptionOIDipForwarding是否作为一个IP网关.1.3.6.1.2.1.4.1ipDefaultTTLIP头中的Time To Live字段的值.1.3.6.1.2.1.4.2ipInReceivesIP层从下层接收的数据报总数.1.3.6.1.2.1.4.3ipInHdrErrors由于IP头出错而丢弃的数据报.1.3.6.1.2.1.4.4ipInAddrErrors地址出错(无效地址、不支持的地址和非本地主机地址)的数据报.1.3.6.1.2.1.4.5ipForwDatagrams已转发的数据报.1.3.6.1.2.1.4.6ipInUnknownProtos不支持数据报的协议,因而被丢弃.1.3.6.1.2.1.4.7ipInDiscards因缺乏缓冲资源而丢弃的数据报.1.3.6.1.2.1.4.8ipInDelivers由IP层提交给上层的数据报.1.3.6.1.2.1.4.9ipOutRequests由IP层交给下层需要发送的数据报,不包括ipForwDatagrams.1.3.6.1.2.1.4.10ipOutDiscards在输出端因缺乏缓冲资源而丢弃的数据报.1.3.6.1.2.1.4.11ipOutNoRoutes没有到达目标的路由而丢弃的数据报.1.3.6.1.2.1.4.12ipReasmTimeout数据段等待重装配的最长时间(秒).1.3.6.1.2.1.4.13ipReasmReqds需要重装配的数据段.1.3.6.1.2.1.4.14ipReasmOKs成功重装配的数据段.1.3.6.1.2.1.4.15ipReasmFails不能重装配的数据段.1.3.6.1.2.1.4.16ipFragOKs分段成功的数据段.1.3.6.1.2.1.4.17ipFragFails不能分段的数据段.1.3.6.1.2.1.4.18ipFragCreates产生的数据报分段数.1.3.6.1.2.1.4.19ipAddrTableIP地址表.1.3.6.1.2.1.4.20ipRouteTableIP路由表.1.3.6.1.2.1.4.21ipNetToMediaTableIP与物理地址转换表.1.3.6.1.2.1.4.22ipRoutingDiscards无效的路由项,包括为释放缓冲空间而丢弃路由项.1.3.6.1.2.1.4.23TCPNameDescriptionOIDtcpRtoAlgorithm重传时间算法.1.3.6.1.2.1.6.1tcpRtoMin重传时间最小值.1.3.6.1.2.1.6.2tcpRtoMax重传时间最大值.1.3.6.1.2.1.6.3tcpMaxConn可建立的最大连接数.1.3.6.1.2.1.6.4tcpActiveOpens主动打开的连接数.1.3.6.1.2.1.6.5tcpPassiveOpens被动打开的连接数.1.3.6.1.2.1.6.6tcpAttemptFails连接建立失败数.1.3.6.1.2.1.6.7tcpEstabResets连接复位数.1.3.6.1.2.1.6.8tcpCurrEstab状态为established或closeWait的连接数.1.3.6.1.2.1.6.9tcpInSegs接收的TCP段总数.1.3.6.1.2.1.6.10tcpOutSegs发送的TCP段总数.1.3.6.1.2.1.6.11tcpRetransSegs重传的TCP段总数.1.3.6.1.2.1.6.12tcpConnTable连接表.1.3.6.1.2.1.6.13tcpInErrors接收的出错TCP段数.1.3.6.1.2.1.6.14tcpOutRests发出的含RST标志的段数.1.3.6.1.2.1.6.15UDPName Description OIDudpInDatagrams 接收的数据报总数 .1.3.6.1.2.1.7.1udpNoPorts 没有发现端口而无法提交的数据报 .1.3.6.1.2.1.7.2udpInErrors 出错的数据报 .1.3.6.1.2.1.7.3udpOutDatagrams 上层协议要求输出的数据报 .1.3.6.1.2.1.7.4udpTable UDP表 .1.3.6.1.2.1.7.5SNMPNameDescriptionOIDsnmpInPktsSNMP模块接收到的分组数.1.3.6.1.2.1.11.1snmpInTotalReqVars被成功读取的Object数,包括get-request和get-next操作.1.3.6.1.2.1.11.13snmpInGetRequestsSNMP模块接收到并处理的get-request的分组数.1.3.6.1.2.1.11.15snmpInGetNextsSNMP模块接收到并处理的get-next的分组数.1.3.6.1.2.1.11.16snmpOutGetResponsesSNMP模块发出的get-responses的分组数.1.3.6.1.2.1.11.28snmpEnableAuthenTraps标记是否允许代理程序产生检验失败警告.1.3.6.1.2.1.11.30 -
-
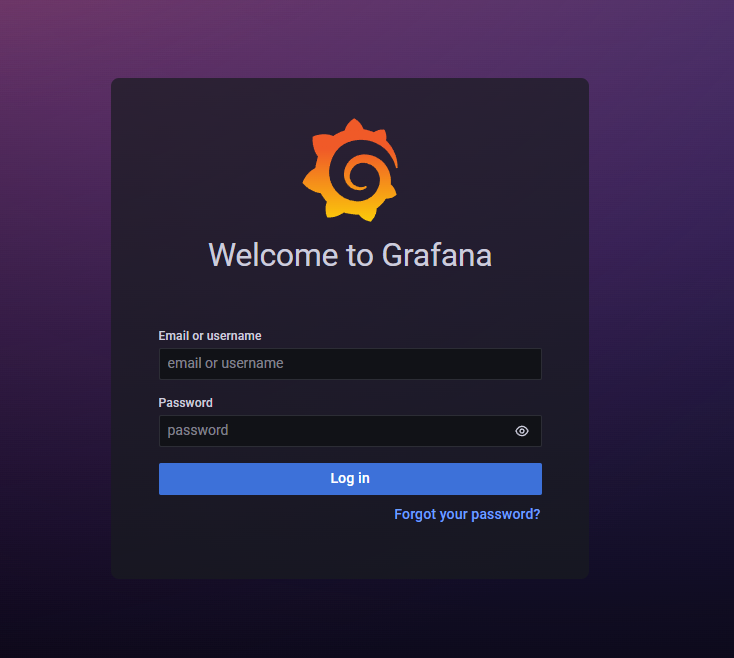
 Zabbix 搭配Grafana绘图 一、 安装Grafana1.1 下载wget https://dl.grafana.com/enterprise/release/grafana-enterprise-8.5.4-1.x86_64.rpm1.2 安装yum install grafana-enterprise-8.5.4-1.x86_64.rpm1.4 启动Grafanasystemctl start grafana-server.service systemctl enable grafana-server.service二、配置Grafana2.1 登录Grafana默认用户名密码为: adminhttp://IP:3000/login2.2 安装Zabbix插件2.3 配置Grafana数据源https:/Zabbix服务器IP地址/api_jsonrpc.php2.4 配置仪表盘三、配置NGINX代理grafana编辑 /etc/grafana/grafana.ini 文件 添加以下文件[server] domain = monitor.xxxxxx.com enforce_domain = true root_url = %(protocol)s://%(domain)s/grafana
Zabbix 搭配Grafana绘图 一、 安装Grafana1.1 下载wget https://dl.grafana.com/enterprise/release/grafana-enterprise-8.5.4-1.x86_64.rpm1.2 安装yum install grafana-enterprise-8.5.4-1.x86_64.rpm1.4 启动Grafanasystemctl start grafana-server.service systemctl enable grafana-server.service二、配置Grafana2.1 登录Grafana默认用户名密码为: adminhttp://IP:3000/login2.2 安装Zabbix插件2.3 配置Grafana数据源https:/Zabbix服务器IP地址/api_jsonrpc.php2.4 配置仪表盘三、配置NGINX代理grafana编辑 /etc/grafana/grafana.ini 文件 添加以下文件[server] domain = monitor.xxxxxx.com enforce_domain = true root_url = %(protocol)s://%(domain)s/grafana