搜索到
299
篇与
的结果
-
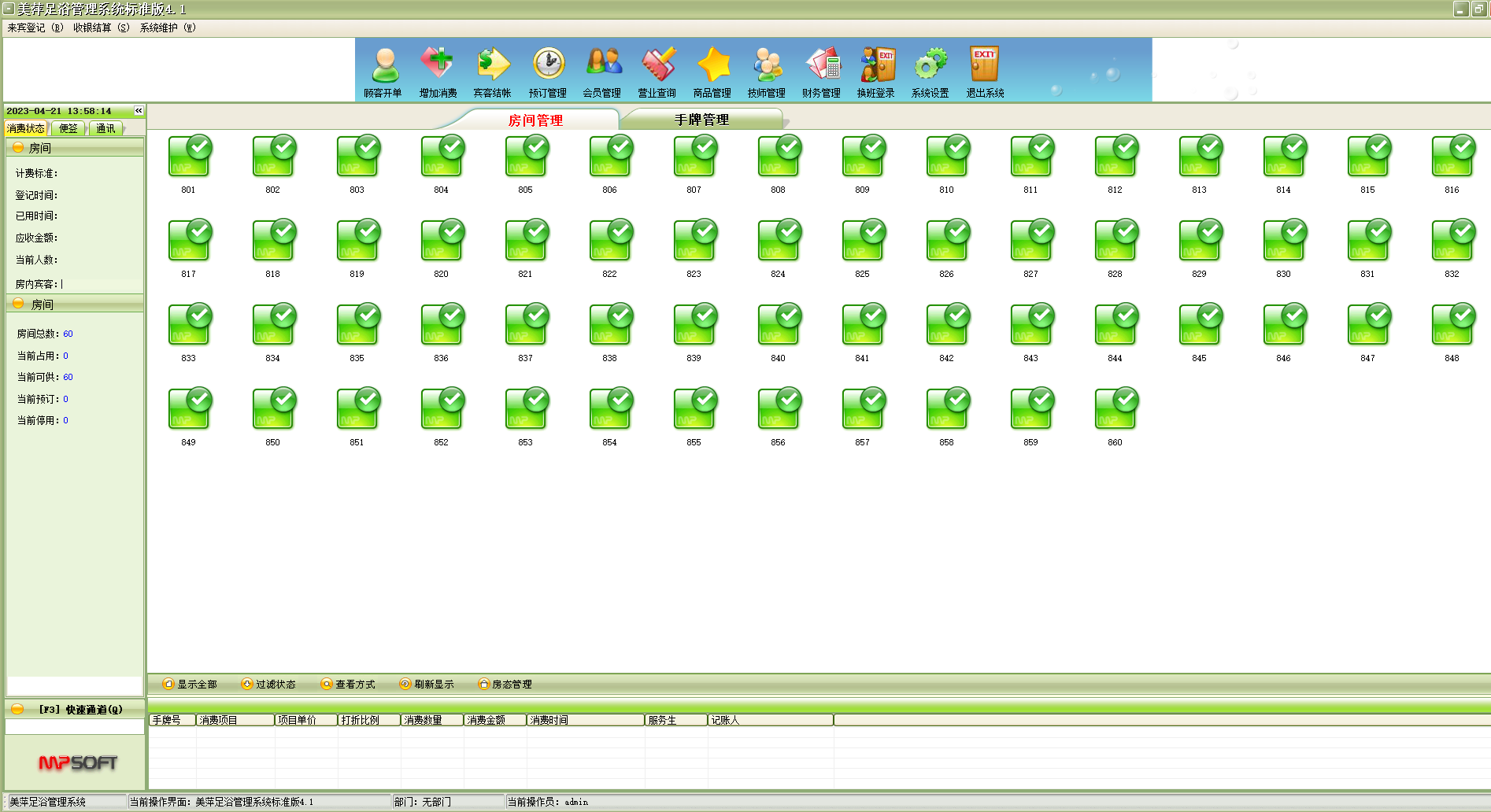
 美萍足浴管理标准破解版 美萍足浴管理标准破解版简介美萍足浴管理系统是一款专业的足浴管理软件,足疗管理系统,它集前台收银管理系统,员工提成管理系统,营业财务报表系统等强大功能为一身,系统界面简洁优美,操作直观简单,无需专门培训即可正常使用。美萍足疗管理软件是一款充分体现了足浴足疗行业的管理实情,为他们量身定做的专业管理软件。美萍沐足管理系统是足浴,足疗企业,酒店宾馆,洗浴桑拿等场所实现管理信息化理想的足浴管理软件。。 适用对象 广泛适用于足浴,足疗企业,酒店宾馆,洗浴桑拿等场所。 产品优势 1、功能强大的统计报表,营业分析。 2、完善的财务分析功能。 3、完整的供货商管理和客户综合管理。 4、简单实用的库存盘点功能。 5、有着非常完善的会员管理系统,支持磁卡,条码卡等多种卡种类型。 6、支持赠品管理。 7、全套的进销存管理。 8、强大的前台收银系统。美萍足浴管理标准破解版下载地址
美萍足浴管理标准破解版 美萍足浴管理标准破解版简介美萍足浴管理系统是一款专业的足浴管理软件,足疗管理系统,它集前台收银管理系统,员工提成管理系统,营业财务报表系统等强大功能为一身,系统界面简洁优美,操作直观简单,无需专门培训即可正常使用。美萍足疗管理软件是一款充分体现了足浴足疗行业的管理实情,为他们量身定做的专业管理软件。美萍沐足管理系统是足浴,足疗企业,酒店宾馆,洗浴桑拿等场所实现管理信息化理想的足浴管理软件。。 适用对象 广泛适用于足浴,足疗企业,酒店宾馆,洗浴桑拿等场所。 产品优势 1、功能强大的统计报表,营业分析。 2、完善的财务分析功能。 3、完整的供货商管理和客户综合管理。 4、简单实用的库存盘点功能。 5、有着非常完善的会员管理系统,支持磁卡,条码卡等多种卡种类型。 6、支持赠品管理。 7、全套的进销存管理。 8、强大的前台收银系统。美萍足浴管理标准破解版下载地址 -
-
 CentOS 启用BBR CentOS 开启 BBR 加速一. 升级CentOS 内核1.1 导入公钥rpm --import https://www.elrepo.org/RPM-GPG-KEY-elrepo.org1.2 安装elrepo源1.2.1 RHEL-7rpm -Uvh http://www.elrepo.org/elrepo-release-7.0-2.el7.elrepo.noarch.rpm1.2.2 RHEL-8yum install https://www.elrepo.org/elrepo-release-8.el8.elrepo.noarch.rpm1.2.3 RHEL-9yum install https://www.elrepo.org/elrepo-release-9.el9.elrepo.noarch.rpm1.3 安装内核 5.10以上yum --enablerepo=elrepo-kernel install kernel-ml -y1.4 确认是否安装成功rpm -qa | grep kernel输出:kernel-3.10.0-1160.71.1.el7.x86_64kernel-tools-3.10.0-1160.71.1.el7.x86_64kernel-ml-5.18.12-1.el7.elrepo.x86_64kernel-headers-3.10.0-1160.71.1.el7.x86_64kernel-3.10.0-1062.el7.x86_64kernel-devel-3.10.0-1062.el7.x86_64kernel-tools-libs-3.10.0-1160.71.1.el7.x86_64kernel-devel-3.10.0-1160.71.1.el7.x86_641.5 查看可用启动项egrep ^menuentry /etc/grub2.cfg | cut -f 2 -d \'[root@ ~]# egrep ^menuentry /etc/grub2.cfg | cut -f 2 -d \'CentOS Linux (5.18.12-1.el7.elrepo.x86_64) 7 (Core)CentOS Linux (3.10.0-1160.71.1.el7.x86_64) 7 (Core)CentOS Linux (3.10.0-1062.el7.x86_64) 7 (Core)CentOS Linux (0-rescue-d93e9d7030a14fe786947b2903d7a446) 7 (Core)1.5.1 设置引导项顺序,使用新安装内核来引导启动:顺序从0开始grub2-set-default 01.5.2 重启系统reboot二. 配置BBR2.1 修改sysctl 启用 BBRecho "net.core.default_qdisc=fq" >> /etc/sysctl.confecho "net.ipv4.tcp_congestion_control=bbr" >> /etc/sysctl.conf2.2 执行sysctl -p输出[root@ ~]# sysctl -pnet.core.rmem_default = 33554432net.core.rmem_max = 33554432net.ipv4.ip_forward = 1net.core.default_qdisc = fqnet.ipv4.tcp_congestion_control = bbrlsmod |grep bbr输出[root@ ~]# lsmod |grep bbrtcp_bbr 20480 9
CentOS 启用BBR CentOS 开启 BBR 加速一. 升级CentOS 内核1.1 导入公钥rpm --import https://www.elrepo.org/RPM-GPG-KEY-elrepo.org1.2 安装elrepo源1.2.1 RHEL-7rpm -Uvh http://www.elrepo.org/elrepo-release-7.0-2.el7.elrepo.noarch.rpm1.2.2 RHEL-8yum install https://www.elrepo.org/elrepo-release-8.el8.elrepo.noarch.rpm1.2.3 RHEL-9yum install https://www.elrepo.org/elrepo-release-9.el9.elrepo.noarch.rpm1.3 安装内核 5.10以上yum --enablerepo=elrepo-kernel install kernel-ml -y1.4 确认是否安装成功rpm -qa | grep kernel输出:kernel-3.10.0-1160.71.1.el7.x86_64kernel-tools-3.10.0-1160.71.1.el7.x86_64kernel-ml-5.18.12-1.el7.elrepo.x86_64kernel-headers-3.10.0-1160.71.1.el7.x86_64kernel-3.10.0-1062.el7.x86_64kernel-devel-3.10.0-1062.el7.x86_64kernel-tools-libs-3.10.0-1160.71.1.el7.x86_64kernel-devel-3.10.0-1160.71.1.el7.x86_641.5 查看可用启动项egrep ^menuentry /etc/grub2.cfg | cut -f 2 -d \'[root@ ~]# egrep ^menuentry /etc/grub2.cfg | cut -f 2 -d \'CentOS Linux (5.18.12-1.el7.elrepo.x86_64) 7 (Core)CentOS Linux (3.10.0-1160.71.1.el7.x86_64) 7 (Core)CentOS Linux (3.10.0-1062.el7.x86_64) 7 (Core)CentOS Linux (0-rescue-d93e9d7030a14fe786947b2903d7a446) 7 (Core)1.5.1 设置引导项顺序,使用新安装内核来引导启动:顺序从0开始grub2-set-default 01.5.2 重启系统reboot二. 配置BBR2.1 修改sysctl 启用 BBRecho "net.core.default_qdisc=fq" >> /etc/sysctl.confecho "net.ipv4.tcp_congestion_control=bbr" >> /etc/sysctl.conf2.2 执行sysctl -p输出[root@ ~]# sysctl -pnet.core.rmem_default = 33554432net.core.rmem_max = 33554432net.ipv4.ip_forward = 1net.core.default_qdisc = fqnet.ipv4.tcp_congestion_control = bbrlsmod |grep bbr输出[root@ ~]# lsmod |grep bbrtcp_bbr 20480 9 -
 OpenVPN-配置文件 1. Openvpn Server 端配置文件################################################# # Sample OpenVPN 2.0 config file for # # multi-client server. # # # # This file is for the server side # # of a many-clients <-> one-server # # OpenVPN configuration. # # # # OpenVPN also supports # # single-machine <-> single-machine # # configurations (See the Examples page # # on the web site for more info). # # # # This config should work on Windows # # or Linux/BSD systems. Remember on # # Windows to quote pathnames and use # # double backslashes, e.g.: # # "C:\\Program Files\\OpenVPN\\config\\foo.key" # # # # Comments are preceded with '#' or ';' # ################################################# # Which local IP address should OpenVPN # listen on? (optional) ;local a.b.c.d # Which TCP/UDP port should OpenVPN listen on? # If you want to run multiple OpenVPN instances # on the same machine, use a different port # number for each one. You will need to # open up this port on your firewall. port 1194 # TCP or UDP server? proto tcp ;proto udp # "dev tun" will create a routed IP tunnel, # "dev tap" will create an ethernet tunnel. # Use "dev tap0" if you are ethernet bridging # and have precreated a tap0 virtual interface # and bridged it with your ethernet interface. # If you want to control access policies # over the VPN, you must create firewall # rules for the the TUN/TAP interface. # On non-Windows systems, you can give # an explicit unit number, such as tun0. # On Windows, use "dev-node" for this. # On most systems, the VPN will not function # unless you partially or fully disable # the firewall for the TUN/TAP interface. ;dev tap dev tun # Windows needs the TAP-Win32 adapter name # from the Network Connections panel if you # have more than one. On XP SP2 or higher, # you may need to selectively disable the # Windows firewall for the TAP adapter. # Non-Windows systems usually don't need this. ;dev-node MyTap # SSL/TLS root certificate (ca), certificate # (cert), and private key (key). Each client # and the server must have their own cert and # key file. The server and all clients will # use the same ca file. # # See the "easy-rsa" directory for a series # of scripts for generating RSA certificates # and private keys. Remember to use # a unique Common Name for the server # and each of the client certificates. # # Any X509 key management system can be used. # OpenVPN can also use a PKCS #12 formatted key file # (see "pkcs12" directive in man page). ca /etc/openvpn/certs/ca.crt cert /etc/openvpn/certs/server.crt key /etc/openvpn/certs/server.key # This file should be kept secret # Diffie hellman parameters. # Generate your own with: # openssl dhparam -out dh2048.pem 2048 #dh dh2048.pem dh /etc/openvpn/certs/dh.pem # Network topology # Should be subnet (addressing via IP) # unless Windows clients v2.0.9 and lower have to # be supported (then net30, i.e. a /30 per client) # Defaults to net30 (not recommended) ;topology subnet # Configure server mode and supply a VPN subnet # for OpenVPN to draw client addresses from. # The server will take 10.8.0.1 for itself, # the rest will be made available to clients. # Each client will be able to reach the server # on 10.8.0.1. Comment this line out if you are # ethernet bridging. See the man page for more info. server 10.8.0.0 255.255.255.0 # Maintain a record of client <-> virtual IP address # associations in this file. If OpenVPN goes down or # is restarted, reconnecting clients can be assigned # the same virtual IP address from the pool that was # previously assigned. ifconfig-pool-persist /var/log/openvpn/ipp.txt # Configure server mode for ethernet bridging. # You must first use your OS's bridging capability # to bridge the TAP interface with the ethernet # NIC interface. Then you must manually set the # IP/netmask on the bridge interface, here we # assume 10.8.0.4/255.255.255.0. Finally we # must set aside an IP range in this subnet # (start=10.8.0.50 end=10.8.0.100) to allocate # to connecting clients. Leave this line commented # out unless you are ethernet bridging. ;server-bridge 10.8.0.4 255.255.255.0 10.8.0.50 10.8.0.100 # Configure server mode for ethernet bridging # using a DHCP-proxy, where clients talk # to the OpenVPN server-side DHCP server # to receive their IP address allocation # and DNS server addresses. You must first use # your OS's bridging capability to bridge the TAP # interface with the ethernet NIC interface. # Note: this mode only works on clients (such as # Windows), where the client-side TAP adapter is # bound to a DHCP client. ;server-bridge # Push routes to the client to allow it # to reach other private subnets behind # the server. Remember that these # private subnets will also need # to know to route the OpenVPN client # address pool (10.8.0.0/255.255.255.0) # back to the OpenVPN server. ;push "route 192.168.10.0 255.255.255.0" ;push "route 192.168.20.0 255.255.255.0" # To assign specific IP addresses to specific # clients or if a connecting client has a private # subnet behind it that should also have VPN access, # use the subdirectory "ccd" for client-specific # configuration files (see man page for more info). # EXAMPLE: Suppose the client # having the certificate common name "Thelonious" # also has a small subnet behind his connecting # machine, such as 192.168.40.128/255.255.255.248. # First, uncomment out these lines: ;client-config-dir ccd ;route 192.168.40.128 255.255.255.248 # Then create a file ccd/Thelonious with this line: # iroute 192.168.40.128 255.255.255.248 # This will allow Thelonious' private subnet to # access the VPN. This example will only work # if you are routing, not bridging, i.e. you are # using "dev tun" and "server" directives. # EXAMPLE: Suppose you want to give # Thelonious a fixed VPN IP address of 10.9.0.1. # First uncomment out these lines: ;client-config-dir ccd ;route 10.9.0.0 255.255.255.252 # Then add this line to ccd/Thelonious: # ifconfig-push 10.9.0.1 10.9.0.2 # Suppose that you want to enable different # firewall access policies for different groups # of clients. There are two methods: # (1) Run multiple OpenVPN daemons, one for each # group, and firewall the TUN/TAP interface # for each group/daemon appropriately. # (2) (Advanced) Create a script to dynamically # modify the firewall in response to access # from different clients. See man # page for more info on learn-address script. ;learn-address ./script # If enabled, this directive will configure # all clients to redirect their default # network gateway through the VPN, causing # all IP traffic such as web browsing and # and DNS lookups to go through the VPN # (The OpenVPN server machine may need to NAT # or bridge the TUN/TAP interface to the internet # in order for this to work properly). ;push "redirect-gateway def1 bypass-dhcp" push "redirect-gateway def1" # Certain Windows-specific network settings # can be pushed to clients, such as DNS # or WINS server addresses. CAVEAT: # http://openvpn.net/faq.html#dhcpcaveats # The addresses below refer to the public # DNS servers provided by opendns.com. ;push "dhcp-option DNS 208.67.222.222" ;push "dhcp-option DNS 208.67.220.220" push "dhcp-option DNS 8.8.8.8" push "dhcp-option DNS 8.8.8.4" # Uncomment this directive to allow different # clients to be able to "see" each other. # By default, clients will only see the server. # To force clients to only see the server, you # will also need to appropriately firewall the # server's TUN/TAP interface. client-to-client # Uncomment this directive if multiple clients # might connect with the same certificate/key # files or common names. This is recommended # only for testing purposes. For production use, # each client should have its own certificate/key # pair. # # IF YOU HAVE NOT GENERATED INDIVIDUAL # CERTIFICATE/KEY PAIRS FOR EACH CLIENT, # EACH HAVING ITS OWN UNIQUE "COMMON NAME", # UNCOMMENT THIS LINE OUT. ;duplicate-cn # The keepalive directive causes ping-like # messages to be sent back and forth over # the link so that each side knows when # the other side has gone down. # Ping every 10 seconds, assume that remote # peer is down if no ping received during # a 120 second time period. keepalive 10 120 # For extra security beyond that provided # by SSL/TLS, create an "HMAC firewall" # to help block DoS attacks and UDP port flooding. # # Generate with: # openvpn --genkey --secret ta.key # # The server and each client must have # a copy of this key. # The second parameter should be '0' # on the server and '1' on the clients. tls-auth /etc/openvpn/server/certs/ta.key 0 # This file is secret # Select a cryptographic cipher. # This config item must be copied to # the client config file as well. # Note that v2.4 client/server will automatically # negotiate AES-256-GCM in TLS mode. # See also the ncp-cipher option in the manpage cipher AES-256-CBC # Enable compression on the VPN link and push the # option to the client (v2.4+ only, for earlier # versions see below) ;compress lz4-v2 ;push "compress lz4-v2" # For compression compatible with older clients use comp-lzo # If you enable it here, you must also # enable it in the client config file. ;comp-lzo # The maximum number of concurrently connected # clients we want to allow. ;max-clients 100 # It's a good idea to reduce the OpenVPN # daemon's privileges after initialization. # # You can uncomment this out on # non-Windows systems. ;user nobody ;group nogroup # The persist options will try to avoid # accessing certain resources on restart # that may no longer be accessible because # of the privilege downgrade. persist-key persist-tun # Output a short status file showing # current connections, truncated # and rewritten every minute. status /var/log/openvpn/openvpn-status.log # By default, log messages will go to the syslog (or # on Windows, if running as a service, they will go to # the "\Program Files\OpenVPN\log" directory). # Use log or log-append to override this default. # "log" will truncate the log file on OpenVPN startup, # while "log-append" will append to it. Use one # or the other (but not both). ;log /var/log/openvpn/openvpn.log ;log-append /var/log/openvpn/openvpn.log # Set the appropriate level of log # file verbosity. # # 0 is silent, except for fatal errors # 4 is reasonable for general usage # 5 and 6 can help to debug connection problems # 9 is extremely verbose verb 3 # Silence repeating messages. At most 20 # sequential messages of the same message # category will be output to the log. ;mute 20 # Notify the client that when the server restarts so it # can automatically reconnect. explicit-exit-notify 0 crl-verify /etc/openvpn/easyrsa/pki/crl.pem1. Openvpn Client 端配置文件############################################## # Sample client-side OpenVPN 2.0 config file # # for connecting to multi-client server. # # # # This configuration can be used by multiple # # clients, however each client should have # # its own cert and key files. # # # # On Windows, you might want to rename this # # file so it has a .ovpn extension # ############################################## # Specify that we are a client and that we # will be pulling certain config file directives # from the server. client # Use the same setting as you are using on # the server. # On most systems, the VPN will not function # unless you partially or fully disable # the firewall for the TUN/TAP interface. ;dev tap dev tun # Windows needs the TAP-Win32 adapter name # from the Network Connections panel # if you have more than one. On XP SP2, # you may need to disable the firewall # for the TAP adapter. ;dev-node MyTap # Are we connecting to a TCP or # UDP server? Use the same setting as # on the server. proto tcp ;proto udp # The hostname/IP and port of the server. # You can have multiple remote entries # to load balance between the servers. remote my-server-1 1194 ;remote my-server-2 1194 # Choose a random host from the remote # list for load-balancing. Otherwise # try hosts in the order specified. ;remote-random # Keep trying indefinitely to resolve the # host name of the OpenVPN server. Very useful # on machines which are not permanently connected # to the internet such as laptops. resolv-retry infinite # Most clients don't need to bind to # a specific local port number. nobind # Downgrade privileges after initialization (non-Windows only) ;user nobody ;group nogroup # Try to preserve some state across restarts. persist-key persist-tun # If you are connecting through an # HTTP proxy to reach the actual OpenVPN # server, put the proxy server/IP and # port number here. See the man page # if your proxy server requires # authentication. ;http-proxy-retry # retry on connection failures ;http-proxy [proxy server] [proxy port #] # Wireless networks often produce a lot # of duplicate packets. Set this flag # to silence duplicate packet warnings. ;mute-replay-warnings # SSL/TLS parms. # See the server config file for more # description. It's best to use # a separate .crt/.key file pair # for each client. A single ca # file can be used for all clients. ca ca.crt cert username.crt key username.key # Verify server certificate by checking that the # certicate has the correct key usage set. # This is an important precaution to protect against # a potential attack discussed here: # http://openvpn.net/howto.html#mitm # # To use this feature, you will need to generate # your server certificates with the keyUsage set to # digitalSignature, keyEncipherment # and the extendedKeyUsage to # serverAuth # EasyRSA can do this for you. remote-cert-tls server # If a tls-auth key is used on the server # then every client must also have the key. tls-auth ta.key 1 # Select a cryptographic cipher. # If the cipher option is used on the server # then you must also specify it here. # Note that v2.4 client/server will automatically # negotiate AES-256-GCM in TLS mode. # See also the ncp-cipher option in the manpage cipher AES-256-CBC # Enable compression on the VPN link. # Don't enable this unless it is also # enabled in the server config file. #comp-lzo # Set log file verbosity. verb 3 # Silence repeating messages ;mute 203. Openvpn APP 配置[Tips] IOS客户端配置client dev tun ;proto tcp proto udp remote xxx.xxx.xxx.xxx 1194 resolv-retry infinite nobind persist-key persist-tun mute-replay-warnings #ca ca.crt #cert client02.crt #key client02.key remote-cert-tls server #tls-auth ta.key 1 #comp-lzo verb 3 <ca> -----BEGIN CERTIFICATE----- MIIDJDCCAgygAwIBAgIJAMv+3UPUdlJjMA0GCSqGSIb3DQEBCwUAMBExDzANBgNV BAMMBnNlcnZlcjAeFw0yMjA0MjEwOTEzNDJaFw0zMjA0MTgwOTEzNDJaMBExDzAN BgNVBAMMBnNlcnZlcjCCASIwDQYJKoZIhvcNAQEBBQADggEPADCCAQoCggEBAJ3n HQJcnsmqkPJwLEV8YymrH1l7189/sXmJ0sa5mIYIcBKKL5haAQ6rdjRlJtuTDnoA oFJ1+Uf9Qwpxs/Tj4blsfewsSD5WlXGq2htgXZv8jjIiKwpSjN2LImJi0pOuow/v nFYGA58Xtsg4EDCIGF5LWc8L0WdfmkvN+LFvUQtnlzyIJ1haHFJdCNtgxpj8Khsa GDDRX7Nr4abnTAQwEb6jcReAhvrqu/b5CtgQDYBHV6pY1toXwZ8PzFnay4ngQFJA 5KUoFsso4beHl/F7u4O44CH61rJwiPavRKBwbYZt6ySU7mQkJRC1yQkRNV4HKwdB 6DOBdmZ+CDJSfMbkpysCAwEAAaN/MH0wHQYDVR0OBBYEFLcvJFbXdouS61U7FQ+d OTmjS20JMEEGA1UdIwQ6MDiAFLcvJFbXdouS61U7FQ+dOTmjS20JoRWkEzARMQ8w DQYDVQQDDAZzZXJ2ZXKCCQDL/t1D1HZSYzAMBgNVHRMEBTADAQH/MAsGA1UdDwQE AwIBBjANBgkqhkiG9w0BAQsFAAOCAQEAQt6Qxbp2sNc/WtRY7jhLl7J52kMzpoO/ 5MWmqoHZ4IU1yM9hN3KzJIby0d0JgzlWAPvl74RnV3Padu5xSlYeCK8y+EOKuJXx b/CXPloHET5EcGLpZWnhFzTUrG68QUAeP3mwP+rr+2/RTSoYNq8Qu5r8npHjhr40 xH+dLtBZDAOLJcKgi4lgCu8WINCMgPwDd5hAsGD1ul7Lso3xGlHJePt6pV2tM45e BD8vhF59WpShIRYlLqWbRG9glB7IFws024jefCEThSXuPt5M6cSO15pqDkeSjG25 CNtvgMw+VSFeBzvs2hEgY8x08pU2EPn1lhmfolcmRVdg8i0qnJBpRg== -----END CERTIFICATE----- </ca> <cert> -----BEGIN CERTIFICATE----- MIIDQjCCAiqgAwIBAgIRANLIdjgXLZIM++/mhxiBLRYwDQYJKoZIhvcNAQELBQAw ETEPMA0GA1UEAwwGc2VydmVyMB4XDTIyMDQyMTEyNTEwOVoXDTI0MDcyNDEyNTEw OVowEzERMA8GA1UEAwwIY2xpZW50MDIwggEiMA0GCSqGSIb3DQEBAQUAA4IBDwAw ggEKAoIBAQDJgm94AHU2P8NpTTuPIDLCQxT3fqJafi/67Yy2LgTAbif+C/9aUuXC M/wJ4fUcBej82+oga583wfwSECubxAaiJc6hJ8fnXUQ7ZPL4PSUCu8QCCFaJCjMC 1nv8DjCC6R9YX7tAzcWOv3z8kz2Ci4elzQCm1oyhxKJKPAUoANtDPO2/8z2vNmWA 01nMsz3ehWADpVto0WWHM2o1ZCE+Mihx20rSL0c3P1IMWqoXdEllo3E10Tl/d1I1 tPY0DQ/t6BjTSUnmbto41rGHat/sarpg4sznuA1eU+wbJbF0/3kAmK8GRdelGLjs Veq0EWIc5QfU7TAl+majz5cBEp8Lh8gNAgMBAAGjgZIwgY8wCQYDVR0TBAIwADAd BgNVHQ4EFgQUUgrZwhdjvyyLaMdexvU32gKz/+4wQQYDVR0jBDowOIAUty8kVtd2 i5LrVTsVD505OaNLbQmhFaQTMBExDzANBgNVBAMMBnNlcnZlcoIJAMv+3UPUdlJj MBMGA1UdJQQMMAoGCCsGAQUFBwMCMAsGA1UdDwQEAwIHgDANBgkqhkiG9w0BAQsF AAOCAQEAl07HOolF0Hos9oHfcQlztWt+WNHKQBQ/FxVjufwYv8cZRu+eZozrZvZe fA4mgzvPXsDRZlLKqL4zLhsGyEUTcjAdvhh0s7PVqgppWN1pLEozTvhgJ8r8L8ev fRXf7R0bJHPzzqFdBzdnFhZ3D4fnDafEFlXfqpl30TdEP50CRjYHk1U+0PWyl3+l 05SBCvNaF0nrK+gD2VDtIHp17nB6LFdpW03sBmkLCVy9KDhk1Z0zwtoJe8RI98sj 2r/7ApuXh6otEJlaFKZ0ChotJL4QEBM5nVOJNFWCvu34KXJevkhRQYTwlKsjgfDN eDOvxAOxozI1HegVavrl8K70iFUhQw== -----END CERTIFICATE----- </cert> <key> -----BEGIN PRIVATE KEY----- MIIEvgIBADANBgkqhkiG9w0BAQEFAASCBKgwggSkAgEAAoIBAQDJgm94AHU2P8Np TTuPIDLCQxT3fqJafi/67Yy2LgTAbif+C/9aUuXCM/wJ4fUcBej82+ogDwnyIzPe IrubxAaiJc6hJ8fnXUQ7ZPL4PSUCu8QCCFaJCjMC1nv8DjCC6R9YX7tAzcWOv3z8 kz2Ci4elzQCm1oyhxKJKPAUoANtDPO2/8z2vNmWA01nMsz3ehWADpVto0WWHM2o1 ZCE+Mihx20rSL0c3P1IMWqoXdEllo3E10Tl/d1I1tPY0DQ/t6BjTSUnmbto41rGH at/sarpg4sznuA1eU+wbJbF0/3kAmK8GRdelGLjsVeq0EWIc5QfU7TAl+majz5cB Ep8Lh8gNAgMBAAECggEAajhZbdY/8vK1nSJbDN0aJJCb0sJr7mup+wmRLM8hLhZi +mV0mzYraq1gZA052SW8ZN2/klqbEYpA4w1H+5nfLUXkn8qKc4kUWIKkGPqSMdis P64Jf39i2FIbVQhdxgQAw+LioAxX4SFLTxCGUfQe8uUXPNrHktZF/f+ZcDbTXaMm 8Y2FyUBXBXuiDgdFw1cP4ShkMY6bGje1pAJ1gVMDKvGumL5L7XYQBF4idu+oUJvH xgZGbxihMA/MpSQK3qp+0/TjvQ3hyxPnoFaZ2IVWDhsdaTINJ88odBeWx/apYUhJ ZArs29e08h+CCDdm2ahgAysFOvRV9QsMrOz/D96LOQKBgQDldojO+OY6ApL+83D6 dtvPYUd0FZbgeNmmuNmpKvD73u2Ui2GfsJvp4DCyegCrxqMrvNVSCmJDUaYZr0qp M2Osbqksn+g0+SRGxSH8l0HhXJDiDCfIeWIWpma4MCnaMJyDq7Qi53gGG1ErXVC3 YjwhjFS8e7sHO+vrI3J3XnsVOwKBgQDg0E+3Jozfuv9AHUqYGfNg4UOs8kADbVTM uNEBQiEGLGvmXfJj5nwPv5IXlybhCf3pezEjGdosRoFkNgauQ2/L7LokWG6siJaE 3xRzWmHu6U7LNoIRc8kPTqf66tTtu9TJExI5uOVMWLq7KVS72qnlHbneq+kjbjmm JSNz5J2jVwKBgQCy97eOjiyqtBVISkEk6I1aesoLLUeG/lrroSMKwVZBbEcq42cZ 8No6GESC/4sEbyIW2+oZWcX4MXd2cvStcUpdU9YY2wN2RZdYpypx4ttcVSEfXVGu F5Y8ij51jAMojV+Vhtcxng1L3gR56QcqcLDrjZMNiwd9hevkcro1hfhDvwKBgDOq 7Ic1Tu8kdQFxOfGXFT5Qx1L6IggnmnOqji5x2lEm6G17bffTwvODnbnaPU8/EqIU dAiTKnc+hQJZAFQQn6MIdwdfY6A3jBBhjLuuLA/Sgw9lKaOFLtJby3N5gRJaNt83 iNrHSbuwMMpasweffsd23Cp67Av+izVKF8nM4wXlAoGBAMFoEH4QDsU9sCZ/7L9t ZstQJ6zPo/aEyVmVH8aogSmlVGBXTigIfXi33UbTqg93IfVGfL1AS+9Ey8I4jq/w 3RtEqe5jzFTdYakjQns++dMq4+0uLSm8XvEGzOZO6dv+dDHXjr3BXUqVFwyyta0O ERqSBDvaSh5zPEc0VeNrZ4Dp -----END PRIVATE KEY----- </key> key-direction 1 <tls-auth> -----BEGIN OpenVPN Static key V1----- 2c5942c3e9d2bf3ba6841c4dc83ac75b 9d73d8e18c45cfecfb98b6d111223d46 6e7eb7309e891e0966914c479e7db614 e847ebcc1f7364c9b4d12db64915e6e7 62cee3c02bbd11a467bbf3053598e865 bcc4497128d4b14816edf37a16737a58 e0f51f0309863ed6458e68730edfe8de 74e54c593b7278581cb3be0a100b2cf4 dae3e72c521a06a7b3ce2777bb7e0caa 42b4255b5dd05d4d5f0315f3989952fd 06a7acc06209a78fe23841818a02303e 2afe2b70cecc110d18bb8fdcb891fa76 7afc99574047c707e5df5afcba937403 4388a0f8ebfbff63079bf6fae3535c56 88f7d75982d56bc24e4e1ae51286c992 f81b01a21523656458941f19e3a98629 -----END OpenVPN Static key V1----- </tls-auth>
OpenVPN-配置文件 1. Openvpn Server 端配置文件################################################# # Sample OpenVPN 2.0 config file for # # multi-client server. # # # # This file is for the server side # # of a many-clients <-> one-server # # OpenVPN configuration. # # # # OpenVPN also supports # # single-machine <-> single-machine # # configurations (See the Examples page # # on the web site for more info). # # # # This config should work on Windows # # or Linux/BSD systems. Remember on # # Windows to quote pathnames and use # # double backslashes, e.g.: # # "C:\\Program Files\\OpenVPN\\config\\foo.key" # # # # Comments are preceded with '#' or ';' # ################################################# # Which local IP address should OpenVPN # listen on? (optional) ;local a.b.c.d # Which TCP/UDP port should OpenVPN listen on? # If you want to run multiple OpenVPN instances # on the same machine, use a different port # number for each one. You will need to # open up this port on your firewall. port 1194 # TCP or UDP server? proto tcp ;proto udp # "dev tun" will create a routed IP tunnel, # "dev tap" will create an ethernet tunnel. # Use "dev tap0" if you are ethernet bridging # and have precreated a tap0 virtual interface # and bridged it with your ethernet interface. # If you want to control access policies # over the VPN, you must create firewall # rules for the the TUN/TAP interface. # On non-Windows systems, you can give # an explicit unit number, such as tun0. # On Windows, use "dev-node" for this. # On most systems, the VPN will not function # unless you partially or fully disable # the firewall for the TUN/TAP interface. ;dev tap dev tun # Windows needs the TAP-Win32 adapter name # from the Network Connections panel if you # have more than one. On XP SP2 or higher, # you may need to selectively disable the # Windows firewall for the TAP adapter. # Non-Windows systems usually don't need this. ;dev-node MyTap # SSL/TLS root certificate (ca), certificate # (cert), and private key (key). Each client # and the server must have their own cert and # key file. The server and all clients will # use the same ca file. # # See the "easy-rsa" directory for a series # of scripts for generating RSA certificates # and private keys. Remember to use # a unique Common Name for the server # and each of the client certificates. # # Any X509 key management system can be used. # OpenVPN can also use a PKCS #12 formatted key file # (see "pkcs12" directive in man page). ca /etc/openvpn/certs/ca.crt cert /etc/openvpn/certs/server.crt key /etc/openvpn/certs/server.key # This file should be kept secret # Diffie hellman parameters. # Generate your own with: # openssl dhparam -out dh2048.pem 2048 #dh dh2048.pem dh /etc/openvpn/certs/dh.pem # Network topology # Should be subnet (addressing via IP) # unless Windows clients v2.0.9 and lower have to # be supported (then net30, i.e. a /30 per client) # Defaults to net30 (not recommended) ;topology subnet # Configure server mode and supply a VPN subnet # for OpenVPN to draw client addresses from. # The server will take 10.8.0.1 for itself, # the rest will be made available to clients. # Each client will be able to reach the server # on 10.8.0.1. Comment this line out if you are # ethernet bridging. See the man page for more info. server 10.8.0.0 255.255.255.0 # Maintain a record of client <-> virtual IP address # associations in this file. If OpenVPN goes down or # is restarted, reconnecting clients can be assigned # the same virtual IP address from the pool that was # previously assigned. ifconfig-pool-persist /var/log/openvpn/ipp.txt # Configure server mode for ethernet bridging. # You must first use your OS's bridging capability # to bridge the TAP interface with the ethernet # NIC interface. Then you must manually set the # IP/netmask on the bridge interface, here we # assume 10.8.0.4/255.255.255.0. Finally we # must set aside an IP range in this subnet # (start=10.8.0.50 end=10.8.0.100) to allocate # to connecting clients. Leave this line commented # out unless you are ethernet bridging. ;server-bridge 10.8.0.4 255.255.255.0 10.8.0.50 10.8.0.100 # Configure server mode for ethernet bridging # using a DHCP-proxy, where clients talk # to the OpenVPN server-side DHCP server # to receive their IP address allocation # and DNS server addresses. You must first use # your OS's bridging capability to bridge the TAP # interface with the ethernet NIC interface. # Note: this mode only works on clients (such as # Windows), where the client-side TAP adapter is # bound to a DHCP client. ;server-bridge # Push routes to the client to allow it # to reach other private subnets behind # the server. Remember that these # private subnets will also need # to know to route the OpenVPN client # address pool (10.8.0.0/255.255.255.0) # back to the OpenVPN server. ;push "route 192.168.10.0 255.255.255.0" ;push "route 192.168.20.0 255.255.255.0" # To assign specific IP addresses to specific # clients or if a connecting client has a private # subnet behind it that should also have VPN access, # use the subdirectory "ccd" for client-specific # configuration files (see man page for more info). # EXAMPLE: Suppose the client # having the certificate common name "Thelonious" # also has a small subnet behind his connecting # machine, such as 192.168.40.128/255.255.255.248. # First, uncomment out these lines: ;client-config-dir ccd ;route 192.168.40.128 255.255.255.248 # Then create a file ccd/Thelonious with this line: # iroute 192.168.40.128 255.255.255.248 # This will allow Thelonious' private subnet to # access the VPN. This example will only work # if you are routing, not bridging, i.e. you are # using "dev tun" and "server" directives. # EXAMPLE: Suppose you want to give # Thelonious a fixed VPN IP address of 10.9.0.1. # First uncomment out these lines: ;client-config-dir ccd ;route 10.9.0.0 255.255.255.252 # Then add this line to ccd/Thelonious: # ifconfig-push 10.9.0.1 10.9.0.2 # Suppose that you want to enable different # firewall access policies for different groups # of clients. There are two methods: # (1) Run multiple OpenVPN daemons, one for each # group, and firewall the TUN/TAP interface # for each group/daemon appropriately. # (2) (Advanced) Create a script to dynamically # modify the firewall in response to access # from different clients. See man # page for more info on learn-address script. ;learn-address ./script # If enabled, this directive will configure # all clients to redirect their default # network gateway through the VPN, causing # all IP traffic such as web browsing and # and DNS lookups to go through the VPN # (The OpenVPN server machine may need to NAT # or bridge the TUN/TAP interface to the internet # in order for this to work properly). ;push "redirect-gateway def1 bypass-dhcp" push "redirect-gateway def1" # Certain Windows-specific network settings # can be pushed to clients, such as DNS # or WINS server addresses. CAVEAT: # http://openvpn.net/faq.html#dhcpcaveats # The addresses below refer to the public # DNS servers provided by opendns.com. ;push "dhcp-option DNS 208.67.222.222" ;push "dhcp-option DNS 208.67.220.220" push "dhcp-option DNS 8.8.8.8" push "dhcp-option DNS 8.8.8.4" # Uncomment this directive to allow different # clients to be able to "see" each other. # By default, clients will only see the server. # To force clients to only see the server, you # will also need to appropriately firewall the # server's TUN/TAP interface. client-to-client # Uncomment this directive if multiple clients # might connect with the same certificate/key # files or common names. This is recommended # only for testing purposes. For production use, # each client should have its own certificate/key # pair. # # IF YOU HAVE NOT GENERATED INDIVIDUAL # CERTIFICATE/KEY PAIRS FOR EACH CLIENT, # EACH HAVING ITS OWN UNIQUE "COMMON NAME", # UNCOMMENT THIS LINE OUT. ;duplicate-cn # The keepalive directive causes ping-like # messages to be sent back and forth over # the link so that each side knows when # the other side has gone down. # Ping every 10 seconds, assume that remote # peer is down if no ping received during # a 120 second time period. keepalive 10 120 # For extra security beyond that provided # by SSL/TLS, create an "HMAC firewall" # to help block DoS attacks and UDP port flooding. # # Generate with: # openvpn --genkey --secret ta.key # # The server and each client must have # a copy of this key. # The second parameter should be '0' # on the server and '1' on the clients. tls-auth /etc/openvpn/server/certs/ta.key 0 # This file is secret # Select a cryptographic cipher. # This config item must be copied to # the client config file as well. # Note that v2.4 client/server will automatically # negotiate AES-256-GCM in TLS mode. # See also the ncp-cipher option in the manpage cipher AES-256-CBC # Enable compression on the VPN link and push the # option to the client (v2.4+ only, for earlier # versions see below) ;compress lz4-v2 ;push "compress lz4-v2" # For compression compatible with older clients use comp-lzo # If you enable it here, you must also # enable it in the client config file. ;comp-lzo # The maximum number of concurrently connected # clients we want to allow. ;max-clients 100 # It's a good idea to reduce the OpenVPN # daemon's privileges after initialization. # # You can uncomment this out on # non-Windows systems. ;user nobody ;group nogroup # The persist options will try to avoid # accessing certain resources on restart # that may no longer be accessible because # of the privilege downgrade. persist-key persist-tun # Output a short status file showing # current connections, truncated # and rewritten every minute. status /var/log/openvpn/openvpn-status.log # By default, log messages will go to the syslog (or # on Windows, if running as a service, they will go to # the "\Program Files\OpenVPN\log" directory). # Use log or log-append to override this default. # "log" will truncate the log file on OpenVPN startup, # while "log-append" will append to it. Use one # or the other (but not both). ;log /var/log/openvpn/openvpn.log ;log-append /var/log/openvpn/openvpn.log # Set the appropriate level of log # file verbosity. # # 0 is silent, except for fatal errors # 4 is reasonable for general usage # 5 and 6 can help to debug connection problems # 9 is extremely verbose verb 3 # Silence repeating messages. At most 20 # sequential messages of the same message # category will be output to the log. ;mute 20 # Notify the client that when the server restarts so it # can automatically reconnect. explicit-exit-notify 0 crl-verify /etc/openvpn/easyrsa/pki/crl.pem1. Openvpn Client 端配置文件############################################## # Sample client-side OpenVPN 2.0 config file # # for connecting to multi-client server. # # # # This configuration can be used by multiple # # clients, however each client should have # # its own cert and key files. # # # # On Windows, you might want to rename this # # file so it has a .ovpn extension # ############################################## # Specify that we are a client and that we # will be pulling certain config file directives # from the server. client # Use the same setting as you are using on # the server. # On most systems, the VPN will not function # unless you partially or fully disable # the firewall for the TUN/TAP interface. ;dev tap dev tun # Windows needs the TAP-Win32 adapter name # from the Network Connections panel # if you have more than one. On XP SP2, # you may need to disable the firewall # for the TAP adapter. ;dev-node MyTap # Are we connecting to a TCP or # UDP server? Use the same setting as # on the server. proto tcp ;proto udp # The hostname/IP and port of the server. # You can have multiple remote entries # to load balance between the servers. remote my-server-1 1194 ;remote my-server-2 1194 # Choose a random host from the remote # list for load-balancing. Otherwise # try hosts in the order specified. ;remote-random # Keep trying indefinitely to resolve the # host name of the OpenVPN server. Very useful # on machines which are not permanently connected # to the internet such as laptops. resolv-retry infinite # Most clients don't need to bind to # a specific local port number. nobind # Downgrade privileges after initialization (non-Windows only) ;user nobody ;group nogroup # Try to preserve some state across restarts. persist-key persist-tun # If you are connecting through an # HTTP proxy to reach the actual OpenVPN # server, put the proxy server/IP and # port number here. See the man page # if your proxy server requires # authentication. ;http-proxy-retry # retry on connection failures ;http-proxy [proxy server] [proxy port #] # Wireless networks often produce a lot # of duplicate packets. Set this flag # to silence duplicate packet warnings. ;mute-replay-warnings # SSL/TLS parms. # See the server config file for more # description. It's best to use # a separate .crt/.key file pair # for each client. A single ca # file can be used for all clients. ca ca.crt cert username.crt key username.key # Verify server certificate by checking that the # certicate has the correct key usage set. # This is an important precaution to protect against # a potential attack discussed here: # http://openvpn.net/howto.html#mitm # # To use this feature, you will need to generate # your server certificates with the keyUsage set to # digitalSignature, keyEncipherment # and the extendedKeyUsage to # serverAuth # EasyRSA can do this for you. remote-cert-tls server # If a tls-auth key is used on the server # then every client must also have the key. tls-auth ta.key 1 # Select a cryptographic cipher. # If the cipher option is used on the server # then you must also specify it here. # Note that v2.4 client/server will automatically # negotiate AES-256-GCM in TLS mode. # See also the ncp-cipher option in the manpage cipher AES-256-CBC # Enable compression on the VPN link. # Don't enable this unless it is also # enabled in the server config file. #comp-lzo # Set log file verbosity. verb 3 # Silence repeating messages ;mute 203. Openvpn APP 配置[Tips] IOS客户端配置client dev tun ;proto tcp proto udp remote xxx.xxx.xxx.xxx 1194 resolv-retry infinite nobind persist-key persist-tun mute-replay-warnings #ca ca.crt #cert client02.crt #key client02.key remote-cert-tls server #tls-auth ta.key 1 #comp-lzo verb 3 <ca> -----BEGIN CERTIFICATE----- MIIDJDCCAgygAwIBAgIJAMv+3UPUdlJjMA0GCSqGSIb3DQEBCwUAMBExDzANBgNV BAMMBnNlcnZlcjAeFw0yMjA0MjEwOTEzNDJaFw0zMjA0MTgwOTEzNDJaMBExDzAN BgNVBAMMBnNlcnZlcjCCASIwDQYJKoZIhvcNAQEBBQADggEPADCCAQoCggEBAJ3n HQJcnsmqkPJwLEV8YymrH1l7189/sXmJ0sa5mIYIcBKKL5haAQ6rdjRlJtuTDnoA oFJ1+Uf9Qwpxs/Tj4blsfewsSD5WlXGq2htgXZv8jjIiKwpSjN2LImJi0pOuow/v nFYGA58Xtsg4EDCIGF5LWc8L0WdfmkvN+LFvUQtnlzyIJ1haHFJdCNtgxpj8Khsa GDDRX7Nr4abnTAQwEb6jcReAhvrqu/b5CtgQDYBHV6pY1toXwZ8PzFnay4ngQFJA 5KUoFsso4beHl/F7u4O44CH61rJwiPavRKBwbYZt6ySU7mQkJRC1yQkRNV4HKwdB 6DOBdmZ+CDJSfMbkpysCAwEAAaN/MH0wHQYDVR0OBBYEFLcvJFbXdouS61U7FQ+d OTmjS20JMEEGA1UdIwQ6MDiAFLcvJFbXdouS61U7FQ+dOTmjS20JoRWkEzARMQ8w DQYDVQQDDAZzZXJ2ZXKCCQDL/t1D1HZSYzAMBgNVHRMEBTADAQH/MAsGA1UdDwQE AwIBBjANBgkqhkiG9w0BAQsFAAOCAQEAQt6Qxbp2sNc/WtRY7jhLl7J52kMzpoO/ 5MWmqoHZ4IU1yM9hN3KzJIby0d0JgzlWAPvl74RnV3Padu5xSlYeCK8y+EOKuJXx b/CXPloHET5EcGLpZWnhFzTUrG68QUAeP3mwP+rr+2/RTSoYNq8Qu5r8npHjhr40 xH+dLtBZDAOLJcKgi4lgCu8WINCMgPwDd5hAsGD1ul7Lso3xGlHJePt6pV2tM45e BD8vhF59WpShIRYlLqWbRG9glB7IFws024jefCEThSXuPt5M6cSO15pqDkeSjG25 CNtvgMw+VSFeBzvs2hEgY8x08pU2EPn1lhmfolcmRVdg8i0qnJBpRg== -----END CERTIFICATE----- </ca> <cert> -----BEGIN CERTIFICATE----- MIIDQjCCAiqgAwIBAgIRANLIdjgXLZIM++/mhxiBLRYwDQYJKoZIhvcNAQELBQAw ETEPMA0GA1UEAwwGc2VydmVyMB4XDTIyMDQyMTEyNTEwOVoXDTI0MDcyNDEyNTEw OVowEzERMA8GA1UEAwwIY2xpZW50MDIwggEiMA0GCSqGSIb3DQEBAQUAA4IBDwAw ggEKAoIBAQDJgm94AHU2P8NpTTuPIDLCQxT3fqJafi/67Yy2LgTAbif+C/9aUuXC M/wJ4fUcBej82+oga583wfwSECubxAaiJc6hJ8fnXUQ7ZPL4PSUCu8QCCFaJCjMC 1nv8DjCC6R9YX7tAzcWOv3z8kz2Ci4elzQCm1oyhxKJKPAUoANtDPO2/8z2vNmWA 01nMsz3ehWADpVto0WWHM2o1ZCE+Mihx20rSL0c3P1IMWqoXdEllo3E10Tl/d1I1 tPY0DQ/t6BjTSUnmbto41rGHat/sarpg4sznuA1eU+wbJbF0/3kAmK8GRdelGLjs Veq0EWIc5QfU7TAl+majz5cBEp8Lh8gNAgMBAAGjgZIwgY8wCQYDVR0TBAIwADAd BgNVHQ4EFgQUUgrZwhdjvyyLaMdexvU32gKz/+4wQQYDVR0jBDowOIAUty8kVtd2 i5LrVTsVD505OaNLbQmhFaQTMBExDzANBgNVBAMMBnNlcnZlcoIJAMv+3UPUdlJj MBMGA1UdJQQMMAoGCCsGAQUFBwMCMAsGA1UdDwQEAwIHgDANBgkqhkiG9w0BAQsF AAOCAQEAl07HOolF0Hos9oHfcQlztWt+WNHKQBQ/FxVjufwYv8cZRu+eZozrZvZe fA4mgzvPXsDRZlLKqL4zLhsGyEUTcjAdvhh0s7PVqgppWN1pLEozTvhgJ8r8L8ev fRXf7R0bJHPzzqFdBzdnFhZ3D4fnDafEFlXfqpl30TdEP50CRjYHk1U+0PWyl3+l 05SBCvNaF0nrK+gD2VDtIHp17nB6LFdpW03sBmkLCVy9KDhk1Z0zwtoJe8RI98sj 2r/7ApuXh6otEJlaFKZ0ChotJL4QEBM5nVOJNFWCvu34KXJevkhRQYTwlKsjgfDN eDOvxAOxozI1HegVavrl8K70iFUhQw== -----END CERTIFICATE----- </cert> <key> -----BEGIN PRIVATE KEY----- MIIEvgIBADANBgkqhkiG9w0BAQEFAASCBKgwggSkAgEAAoIBAQDJgm94AHU2P8Np TTuPIDLCQxT3fqJafi/67Yy2LgTAbif+C/9aUuXCM/wJ4fUcBej82+ogDwnyIzPe IrubxAaiJc6hJ8fnXUQ7ZPL4PSUCu8QCCFaJCjMC1nv8DjCC6R9YX7tAzcWOv3z8 kz2Ci4elzQCm1oyhxKJKPAUoANtDPO2/8z2vNmWA01nMsz3ehWADpVto0WWHM2o1 ZCE+Mihx20rSL0c3P1IMWqoXdEllo3E10Tl/d1I1tPY0DQ/t6BjTSUnmbto41rGH at/sarpg4sznuA1eU+wbJbF0/3kAmK8GRdelGLjsVeq0EWIc5QfU7TAl+majz5cB Ep8Lh8gNAgMBAAECggEAajhZbdY/8vK1nSJbDN0aJJCb0sJr7mup+wmRLM8hLhZi +mV0mzYraq1gZA052SW8ZN2/klqbEYpA4w1H+5nfLUXkn8qKc4kUWIKkGPqSMdis P64Jf39i2FIbVQhdxgQAw+LioAxX4SFLTxCGUfQe8uUXPNrHktZF/f+ZcDbTXaMm 8Y2FyUBXBXuiDgdFw1cP4ShkMY6bGje1pAJ1gVMDKvGumL5L7XYQBF4idu+oUJvH xgZGbxihMA/MpSQK3qp+0/TjvQ3hyxPnoFaZ2IVWDhsdaTINJ88odBeWx/apYUhJ ZArs29e08h+CCDdm2ahgAysFOvRV9QsMrOz/D96LOQKBgQDldojO+OY6ApL+83D6 dtvPYUd0FZbgeNmmuNmpKvD73u2Ui2GfsJvp4DCyegCrxqMrvNVSCmJDUaYZr0qp M2Osbqksn+g0+SRGxSH8l0HhXJDiDCfIeWIWpma4MCnaMJyDq7Qi53gGG1ErXVC3 YjwhjFS8e7sHO+vrI3J3XnsVOwKBgQDg0E+3Jozfuv9AHUqYGfNg4UOs8kADbVTM uNEBQiEGLGvmXfJj5nwPv5IXlybhCf3pezEjGdosRoFkNgauQ2/L7LokWG6siJaE 3xRzWmHu6U7LNoIRc8kPTqf66tTtu9TJExI5uOVMWLq7KVS72qnlHbneq+kjbjmm JSNz5J2jVwKBgQCy97eOjiyqtBVISkEk6I1aesoLLUeG/lrroSMKwVZBbEcq42cZ 8No6GESC/4sEbyIW2+oZWcX4MXd2cvStcUpdU9YY2wN2RZdYpypx4ttcVSEfXVGu F5Y8ij51jAMojV+Vhtcxng1L3gR56QcqcLDrjZMNiwd9hevkcro1hfhDvwKBgDOq 7Ic1Tu8kdQFxOfGXFT5Qx1L6IggnmnOqji5x2lEm6G17bffTwvODnbnaPU8/EqIU dAiTKnc+hQJZAFQQn6MIdwdfY6A3jBBhjLuuLA/Sgw9lKaOFLtJby3N5gRJaNt83 iNrHSbuwMMpasweffsd23Cp67Av+izVKF8nM4wXlAoGBAMFoEH4QDsU9sCZ/7L9t ZstQJ6zPo/aEyVmVH8aogSmlVGBXTigIfXi33UbTqg93IfVGfL1AS+9Ey8I4jq/w 3RtEqe5jzFTdYakjQns++dMq4+0uLSm8XvEGzOZO6dv+dDHXjr3BXUqVFwyyta0O ERqSBDvaSh5zPEc0VeNrZ4Dp -----END PRIVATE KEY----- </key> key-direction 1 <tls-auth> -----BEGIN OpenVPN Static key V1----- 2c5942c3e9d2bf3ba6841c4dc83ac75b 9d73d8e18c45cfecfb98b6d111223d46 6e7eb7309e891e0966914c479e7db614 e847ebcc1f7364c9b4d12db64915e6e7 62cee3c02bbd11a467bbf3053598e865 bcc4497128d4b14816edf37a16737a58 e0f51f0309863ed6458e68730edfe8de 74e54c593b7278581cb3be0a100b2cf4 dae3e72c521a06a7b3ce2777bb7e0caa 42b4255b5dd05d4d5f0315f3989952fd 06a7acc06209a78fe23841818a02303e 2afe2b70cecc110d18bb8fdcb891fa76 7afc99574047c707e5df5afcba937403 4388a0f8ebfbff63079bf6fae3535c56 88f7d75982d56bc24e4e1ae51286c992 f81b01a21523656458941f19e3a98629 -----END OpenVPN Static key V1----- </tls-auth> -
 Kingdee-常用数据表 一、金蝶云星空常用数据表数据表命名基本规则|表名前缀: t_ 或者 T_视图前缀: v_ 或者 V_多语言表后缀: _L关联关系表后缀: _LK1.1 元数据描述表名元数据t_meta_objectType元数据扩展信息表t_meta_objectType_E元数据缓存表T_META_OBJECTTYPECACHE元数据视图表T_META_OBJECTTYPEVIEW元数据视图V_META_OBJECTTYPE_L元数据扩展多语言名称T_META_OBJECTTYPENAMEEX_L元数据序号T_META_OBJECTTYPE_E基础资料元数据信息表T_META_LOOKUPCLASS基础资料元数据类型表T_META_BASEDATATYPE单据类型表T_BAS_BILLTYPE,T_BAS_BILLTYPEFLDCTL枚举元数据表T_META_FORMENUM枚举项元数据表T_META_FORMENUMITEM转换规则元数据表T_META_CONVERTRULE反写规则元数据表t_bf_writebackrule反写规则扩展表t_BF_WriteBackRuleCust表单和表关系表T_META_TRACKERBILLTABLE领域模型T_MDL_DOMAINMODETYPE领域子模型T_MDL_DOMAINMODELSUB_L元素T_MDL_ELEMENTTYPE元素分组T_MDL_ELEMENTGROUP_L属性T_MDL_ELEMENTPROPERTY领域元素T_MDL_DOMAINMODELELEMENTMAP领域元素属性T_MDL_DOMAINMODELELPROPMAP表单服务T_MDL_FORMBUSINESS操作函数T_MDL_FORMFUNCTION操作T_MDL_FORMOPERATIONTYPE校验T_MDL_FORMVALIDATIONTYPE1.2 弹性域相关表描述表名辅助属性维度定义T_BD_FLEXAUXPROPERTY辅助属性数据表T_BD_FLEXSITEMDETAILV仓位值集表维度定义t_bas_flexValues仓位值集表维度仓位定义T_BAS_FLEXVALUESENTRY仓位值集数据表t_bas_flexValuesDetail核算维度维度定义T_BD_FLEXITEMPROPERTY核算维度数据表T_BD_FLEXITEMDETAILV1.3 菜单描述表名子系统分组T_META_TOPCLASS子系统T_META_SUBSYSTEM_L模块T_META_CONSOLESUBFUNC_L菜单T_META_CONSOLEDETAIL1.4 权限描述表名对象权限T_SEC_OBJECTTYPEPERMISSION权限表T_SEC_FIELDPERMISSION权限项表t_sec_permissionItem功能权限表T_SEC_FUNCPERMISSION功能权限项表T_SEC_FUNCPERMISSIONENTRY字段权限表T_SEC_FIELDPERMISSION字段权限项表T_SEC_FIELDPERMISSIONENTRY用户组织表T_SEC_USERORG角色表T_SEC_ROLE1.5 基础资料描述表名基础资料和表T_META_LOOKUPCLASS组织表T_ORG_ORGANIZATIONS物料T_BD_MATERIAL采购价目表t_PUR_PriceList采购价目分发表t_PUR_PriceList_Issue用户表T_SEC_USER部门表T_BD_DEPARTMENT员工信息表T_BD_STAFF员工任职信息表T_BD_STAFFPOSTINFO业务员表T_BD_OPERATOR业务员分录表T_BD_OPERATORENTRY销售员表V_BD_SALESMAN销售员单据体表V_BD_SALESMANENTRY岗位信息表T_ORG_POST\HR_ORG_HRPOST岗位对应角色表T_ORG_POSTROLE辅助资料表T_BAS_ASSISTANTDATAENTRY辅助资料类别表T_BAS_ASSISTANTDATA基础资料分配表T_ORG_BASEDATAALLOCATEENTRY仓库T_BD_Stock供应商t_BD_Supplier1.6 网控描述表名网控对象表T_BAS_NETWORKCTRLOBJECT互斥对象表T_BAS_NETWORKCTRLMUTEX网络控制表T_BAS_MUTEX网控记录表T_BAS_NETWORKCTRLRECORDS1.7 参数描述表名用户参数表T_BAS_UserParameter系统参数表T_BAS_SysParameter发布参数表T_BAS_ReleaseParameter单据参数表t_BAS_BillGlobalParameter用户界面参数T_BAS_FormParameter1.8 服务描述表名表单服务表T_MDL_FORMBUSINESS操作服务表T_MDL_FORMOPERATIONTYPE校验器表T_MDL_FORMVALIDATIONTYPE1.9 日志描述表名记录引出记录表T_BAS_EXPORTRECORD上机操作日志表t_bas_operateLog上机操作日志备份表t_bas_operateLogBK系统日志表T_BAS_LOG执行计划日志表T_BAS_SCHEDULELOGWebApi日志T_BAS_WEBAPILOG1.10 管理中心描述表名数据中心表T_BAS_DATACENTER补丁日志表表t_bos_installedpackagehis1.11 业务流程图描述表名业务流程版本表T_BF_DEFVERSION业务流程发布表t_BF_Publish业务流程发布分录表t_BF_PublishEntry(流程跟单据类型的关系)业务流程定义单据检索表T_BF_DEFVERSIONLOOKUP(流程跟表的关系)业务流程定义表T_BF_PROCDEF数据中心表T_BAS_DATACENTER1.12 反写描述表名反写规则元数据表t_bf_writebackrule反写规则元数据扩展表t_BF_WriteBackRuleCust反写记录表t_bf_instanceSnap反写记录历史表t_bf_instanceSnapHis反写记录归档表t_bf_SnapBackUp反写日志表T_BF_WBLOG1.13 业务流程实例描述表名业务流程实例表t_BF_Instance业务流程节点表t_BF_InstanceEntry业务流程控制字段反写记录表t_bf_instanceAmount业务流程实例历史表t_bf_instanceHis业务流程节点历史表t_bf_instanceEntryHis业务流程控制字段反写记录历史表t_bf_instanceAmountHis业务流程实例归档表t_bf_instBackUp业务流程节点归档表t_bf_instEntryBackUp业务流程控制字段反写记录归档表t_bf_instAmountBackUp业务流程压缩文件日志表t_bf_InstArchiveLog业务流程压缩文件表t_BF_ArchiveFiles1.14 过滤方案描述表名过滤方案表T_BAS_FILTERSCHEME万能报表默认过滤T_BOS_DEVREPORTDATASOURCE1.15 单据销售描述表名订单表T_SAL_ORDER销售订单明细表T_SAL_ORDERENTRY销售出库单表T_SAL_OUTSTOCK销售出库单明细表T_SAL_OUTSTOCKENTRY应收单表t_AR_receivable应收单明细表t_AR_receivableEntry应付单表T_AP_PAYABLE应付单明细表T_AP_PAYABLEENTRY采购订单表t_PUR_POOrder采购订单明细表t_PUR_POOrderEntry生产订单表PRD_MO、T_PRD_MO工序计划表T_SFC_OPERPLANNING工序计划系列表T_SFC_OPERPLANNINGSEQ工序汇报表T_SFC_OPTRPTENTRY工序转移表T_SFC_OPERATIONTRANSFER生成入库单PRD_INSTOCK 、T_PRD_INSTOCK付款申请单T_CN_PAYAPPLY1.16 附件和附件信息描述表名附件信息T_BAS_FileServerFileInfo附件跟单据关系表T_BAS_ATTACHMENT1.17 报表描述表名关键字T_MDL_RPTKEYWORDS1.18 工作流和审批流描述表名流程定义t_WF_ProcDef版本t_wf_DefVersion流程类型t_WF_ProcessType流程模板t_WF_Template流程发起配置t_wf_prclaunchconfig、T_WF_PRCLAUNCHCONFIG_L流程实例和单据关系t_WF_PiBiMap流程实例T_WF_PROCINST流程节点实例T_WF_ACTINST流程任务T_WF_ASSIGN流程任务接收人T_WF_RECEIVER流程任务详情T_WF_APPROVALASSIGN流程任务处理记录T_WF_APPROVALITEM流程反馈信息表T_WF_DISCUSS1.19 其他描述表名临时表T_BAS_TEMPORARYTABLENAME单据类型T_BAS_BILLTYPE安装包t_bos_installedpackage
Kingdee-常用数据表 一、金蝶云星空常用数据表数据表命名基本规则|表名前缀: t_ 或者 T_视图前缀: v_ 或者 V_多语言表后缀: _L关联关系表后缀: _LK1.1 元数据描述表名元数据t_meta_objectType元数据扩展信息表t_meta_objectType_E元数据缓存表T_META_OBJECTTYPECACHE元数据视图表T_META_OBJECTTYPEVIEW元数据视图V_META_OBJECTTYPE_L元数据扩展多语言名称T_META_OBJECTTYPENAMEEX_L元数据序号T_META_OBJECTTYPE_E基础资料元数据信息表T_META_LOOKUPCLASS基础资料元数据类型表T_META_BASEDATATYPE单据类型表T_BAS_BILLTYPE,T_BAS_BILLTYPEFLDCTL枚举元数据表T_META_FORMENUM枚举项元数据表T_META_FORMENUMITEM转换规则元数据表T_META_CONVERTRULE反写规则元数据表t_bf_writebackrule反写规则扩展表t_BF_WriteBackRuleCust表单和表关系表T_META_TRACKERBILLTABLE领域模型T_MDL_DOMAINMODETYPE领域子模型T_MDL_DOMAINMODELSUB_L元素T_MDL_ELEMENTTYPE元素分组T_MDL_ELEMENTGROUP_L属性T_MDL_ELEMENTPROPERTY领域元素T_MDL_DOMAINMODELELEMENTMAP领域元素属性T_MDL_DOMAINMODELELPROPMAP表单服务T_MDL_FORMBUSINESS操作函数T_MDL_FORMFUNCTION操作T_MDL_FORMOPERATIONTYPE校验T_MDL_FORMVALIDATIONTYPE1.2 弹性域相关表描述表名辅助属性维度定义T_BD_FLEXAUXPROPERTY辅助属性数据表T_BD_FLEXSITEMDETAILV仓位值集表维度定义t_bas_flexValues仓位值集表维度仓位定义T_BAS_FLEXVALUESENTRY仓位值集数据表t_bas_flexValuesDetail核算维度维度定义T_BD_FLEXITEMPROPERTY核算维度数据表T_BD_FLEXITEMDETAILV1.3 菜单描述表名子系统分组T_META_TOPCLASS子系统T_META_SUBSYSTEM_L模块T_META_CONSOLESUBFUNC_L菜单T_META_CONSOLEDETAIL1.4 权限描述表名对象权限T_SEC_OBJECTTYPEPERMISSION权限表T_SEC_FIELDPERMISSION权限项表t_sec_permissionItem功能权限表T_SEC_FUNCPERMISSION功能权限项表T_SEC_FUNCPERMISSIONENTRY字段权限表T_SEC_FIELDPERMISSION字段权限项表T_SEC_FIELDPERMISSIONENTRY用户组织表T_SEC_USERORG角色表T_SEC_ROLE1.5 基础资料描述表名基础资料和表T_META_LOOKUPCLASS组织表T_ORG_ORGANIZATIONS物料T_BD_MATERIAL采购价目表t_PUR_PriceList采购价目分发表t_PUR_PriceList_Issue用户表T_SEC_USER部门表T_BD_DEPARTMENT员工信息表T_BD_STAFF员工任职信息表T_BD_STAFFPOSTINFO业务员表T_BD_OPERATOR业务员分录表T_BD_OPERATORENTRY销售员表V_BD_SALESMAN销售员单据体表V_BD_SALESMANENTRY岗位信息表T_ORG_POST\HR_ORG_HRPOST岗位对应角色表T_ORG_POSTROLE辅助资料表T_BAS_ASSISTANTDATAENTRY辅助资料类别表T_BAS_ASSISTANTDATA基础资料分配表T_ORG_BASEDATAALLOCATEENTRY仓库T_BD_Stock供应商t_BD_Supplier1.6 网控描述表名网控对象表T_BAS_NETWORKCTRLOBJECT互斥对象表T_BAS_NETWORKCTRLMUTEX网络控制表T_BAS_MUTEX网控记录表T_BAS_NETWORKCTRLRECORDS1.7 参数描述表名用户参数表T_BAS_UserParameter系统参数表T_BAS_SysParameter发布参数表T_BAS_ReleaseParameter单据参数表t_BAS_BillGlobalParameter用户界面参数T_BAS_FormParameter1.8 服务描述表名表单服务表T_MDL_FORMBUSINESS操作服务表T_MDL_FORMOPERATIONTYPE校验器表T_MDL_FORMVALIDATIONTYPE1.9 日志描述表名记录引出记录表T_BAS_EXPORTRECORD上机操作日志表t_bas_operateLog上机操作日志备份表t_bas_operateLogBK系统日志表T_BAS_LOG执行计划日志表T_BAS_SCHEDULELOGWebApi日志T_BAS_WEBAPILOG1.10 管理中心描述表名数据中心表T_BAS_DATACENTER补丁日志表表t_bos_installedpackagehis1.11 业务流程图描述表名业务流程版本表T_BF_DEFVERSION业务流程发布表t_BF_Publish业务流程发布分录表t_BF_PublishEntry(流程跟单据类型的关系)业务流程定义单据检索表T_BF_DEFVERSIONLOOKUP(流程跟表的关系)业务流程定义表T_BF_PROCDEF数据中心表T_BAS_DATACENTER1.12 反写描述表名反写规则元数据表t_bf_writebackrule反写规则元数据扩展表t_BF_WriteBackRuleCust反写记录表t_bf_instanceSnap反写记录历史表t_bf_instanceSnapHis反写记录归档表t_bf_SnapBackUp反写日志表T_BF_WBLOG1.13 业务流程实例描述表名业务流程实例表t_BF_Instance业务流程节点表t_BF_InstanceEntry业务流程控制字段反写记录表t_bf_instanceAmount业务流程实例历史表t_bf_instanceHis业务流程节点历史表t_bf_instanceEntryHis业务流程控制字段反写记录历史表t_bf_instanceAmountHis业务流程实例归档表t_bf_instBackUp业务流程节点归档表t_bf_instEntryBackUp业务流程控制字段反写记录归档表t_bf_instAmountBackUp业务流程压缩文件日志表t_bf_InstArchiveLog业务流程压缩文件表t_BF_ArchiveFiles1.14 过滤方案描述表名过滤方案表T_BAS_FILTERSCHEME万能报表默认过滤T_BOS_DEVREPORTDATASOURCE1.15 单据销售描述表名订单表T_SAL_ORDER销售订单明细表T_SAL_ORDERENTRY销售出库单表T_SAL_OUTSTOCK销售出库单明细表T_SAL_OUTSTOCKENTRY应收单表t_AR_receivable应收单明细表t_AR_receivableEntry应付单表T_AP_PAYABLE应付单明细表T_AP_PAYABLEENTRY采购订单表t_PUR_POOrder采购订单明细表t_PUR_POOrderEntry生产订单表PRD_MO、T_PRD_MO工序计划表T_SFC_OPERPLANNING工序计划系列表T_SFC_OPERPLANNINGSEQ工序汇报表T_SFC_OPTRPTENTRY工序转移表T_SFC_OPERATIONTRANSFER生成入库单PRD_INSTOCK 、T_PRD_INSTOCK付款申请单T_CN_PAYAPPLY1.16 附件和附件信息描述表名附件信息T_BAS_FileServerFileInfo附件跟单据关系表T_BAS_ATTACHMENT1.17 报表描述表名关键字T_MDL_RPTKEYWORDS1.18 工作流和审批流描述表名流程定义t_WF_ProcDef版本t_wf_DefVersion流程类型t_WF_ProcessType流程模板t_WF_Template流程发起配置t_wf_prclaunchconfig、T_WF_PRCLAUNCHCONFIG_L流程实例和单据关系t_WF_PiBiMap流程实例T_WF_PROCINST流程节点实例T_WF_ACTINST流程任务T_WF_ASSIGN流程任务接收人T_WF_RECEIVER流程任务详情T_WF_APPROVALASSIGN流程任务处理记录T_WF_APPROVALITEM流程反馈信息表T_WF_DISCUSS1.19 其他描述表名临时表T_BAS_TEMPORARYTABLENAME单据类型T_BAS_BILLTYPE安装包t_bos_installedpackage